
What is Cyber Incident Response? A Guided Overview
Cybersecurity incidents around the globe are making headlines almost daily. In the current situation, where cyber threats evolve rapidly, the ability to respond confidently, rather
Our unique program allows our graduates to lead their peers to strategically and effectively manage cybersecurity risks in their organizations.


Cybersecurity incidents around the globe are making headlines almost daily. In the current situation, where cyber threats evolve rapidly, the ability to respond confidently, rather

Let Recruiters on LinkedIn Know That You’ve Graduated First of all, congratulations! Earning your degree is a landmark achievement. It means you’ve now opened the

Cyber threats are growing at a fast pace, and so is the demand for specialized and skilled cybersecurity professionals. So, for those of you looking

In the world of the Internet and digitization, passwords are the first line of defense between your digital assets and cybercriminals. Yet weak or reused passwords remain among the most significant reasons behind data breaches,

Healthcare Data: What it is and Why it’s Important to Protect it Healthcare data is among the most sensitive categories of information. It includes electronic
What Are Military Tuition Assistance and GI Bill® Education Benefits? For U.S. Military members and veterans, education benefits can dramatically reduce or eliminate the cost

What Are Cybersecurity Certifications? Cybersecurity remains one of the most critical and future-proof career paths available today. Whether you’re a seasoned cybersecurity professional looking to

Cybersecurity has become one of the most critical and in-demand career fields across industries. Cybersecurity is no longer a niche reserved for large tech companies.

Cybersecurity Jobs are More Important Than Ever The cybersecurity industry is experiencing unprecedented growth — and for good reason. Organizations worldwide constantly face complex digital

Why Should You Get a Master’s in Cybersecurity Degree in 2026? Cybercrime has become almost a daily reality. As we move deeper into 2026, organizations
With governments, technology giants, and research institutions worldwide investing heavily in quantum computing innovation, cybersecurity leaders are preparing for one of the largest cryptographic transitions

Cybersecurity education has a problem. The threats changed. For years, security programs have trained professionals to recognize known attack patterns, patch known vulnerabilities, and respond

Why Cybersecurity and Data Center Expansion Go Hand-in-Hand Thanks to artificial intelligence (AI), cloud computing, IoT, remote work, streaming services, and digital transformation initiatives, organizations

There is no finish line in cybersecurity education. A master’s degree is a strong foundation. The field you graduate into will not be the same

Transitioning from military service to a civilian career can feel overwhelming. But in cybersecurity, veterans already possess many of the qualities that the industry urgently

Most cybersecurity job listings today aren’t just asking for security awareness. They want engineers who can read code, architects who understand threat surfaces, and developers

Becoming A CISO – Then Vs. Now For years, the career path to becoming a Chief Information Security Officer (CISO) looked fairly predictable. Gain experience
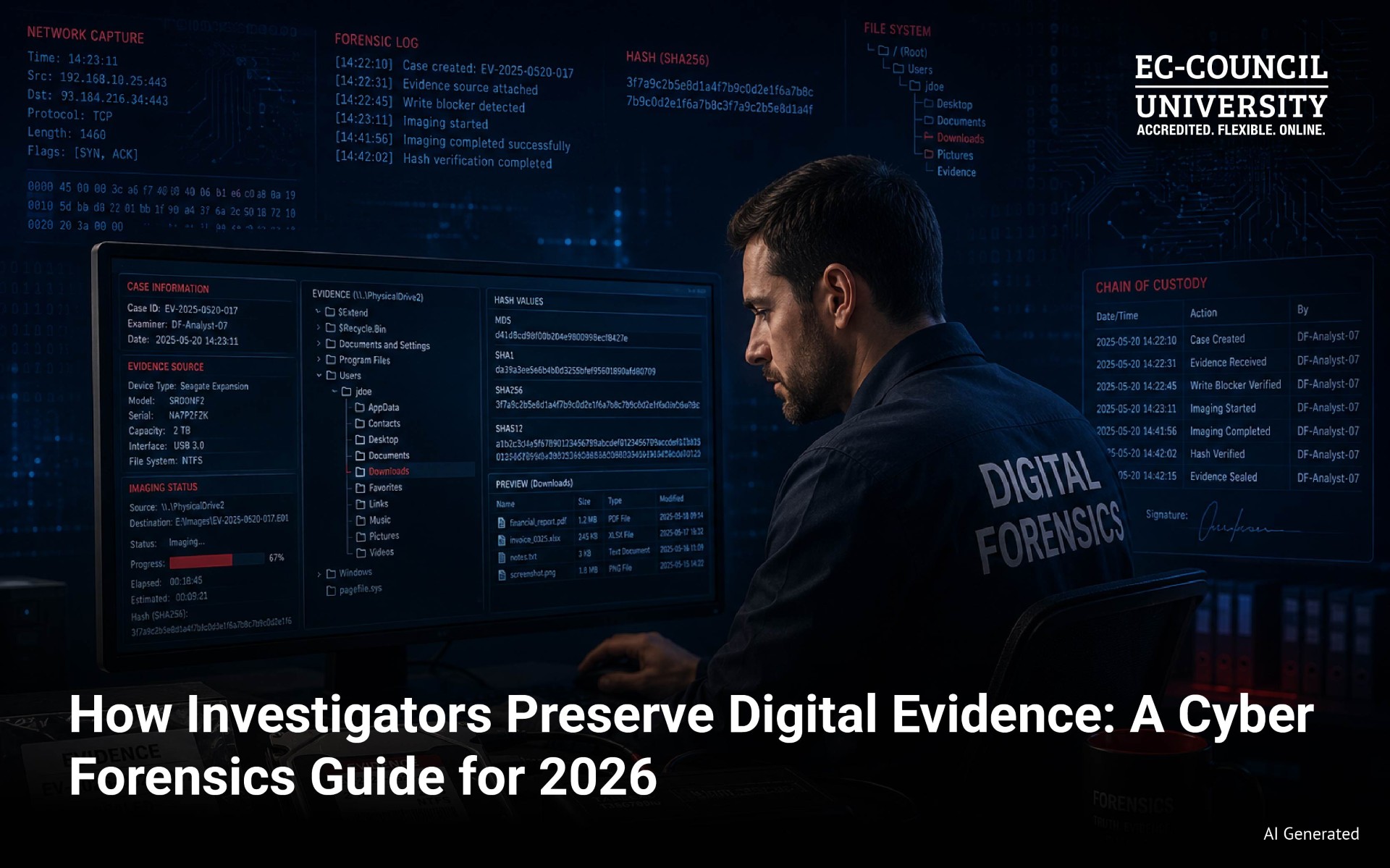
When digital evidence enters an investigation, the clock starts immediately. Every action taken on a device, every file opened, every second of delay changes what

Cybersecurity is no longer a field where broad knowledge carries you to the top. The roles commanding serious compensation in 2026 belong to specialists. Security

Digital forensics has moved well beyond the crime lab. Today it serves incident response teams, litigation support, and corporate intelligence. Organizations in finance, healthcare, and
Introduction (ICYMI): Escalation, Perception, and the Limits of Control Part 2 examined how cyber conflict extends beyond the digital domain into real-world consequences. We learned that cyber operations are not confined to networks. They can affect critical infrastructure, financial systems, and even physical assets. The Stuxnet example demonstrated that cyber....
Introduction (ICYMI): From Deterrence Breakdown to Continuous Cyber Competition Before examining how cyber conflict escalates, it’s important to revisit the foundation established in Part 1. Traditional deterrence theory assumes a world of clarity, where actors can be identified, intentions are visible, and consequences are predictable. In cyberspace, those assumptions begin....
Cyber Conflict Beyond the Technical Lens Cyber conflict is often framed as a technical issue, centered on vulnerabilities, exploits, and defensive tools. But this perspective misses the bigger picture. Cyber operations are strategic instruments of statecraft, embedded in: Political competition Military planning Global security dynamics To understand their true impact,....
There are 1,757 data breaches each minute. By the time you finish reading this article, thousands of data breaches will have occurred. A person, organization, or government directs most. Local governments struggle to keep up with new technologies for better service in exchange for the risk of a cyber attack....
Responding to cyber threats has become a high priority for organizations of all sizes, especially those in financial services. Cybersecurity is a vital element in preventing cyberattacks, as established in the good practices report published by the Financial Industry Regulatory Authority (FINRA). It is an institution that regulates the activity....
In the rapidly evolving digital landscape, cybersecurity has emerged as a critical concern for organizations across all industries. Understanding and addressing cybersecurity risks is essential for protecting data and ensuring the resilience and continuity of business operations. As a faculty member specializing in human resources, change management, and business continuity....

The demand for cybersecurity professionals has reached unprecedented heights. With the constant proliferation of cyber threats and the crucial need to safeguard sensitive data, there’s a significant shortage of skilled cybersecurity experts. You’re on the right track if you’re considering a career in this dynamic field. This blog is your

1. How does cloud technology help to secure a remote workforce compared to traditional on-premises solutions? Cloud technology has the ability to adapt quicker to changes needed to secure workloads. It can spin up new services/servers to account for increased load during demand. It can also be more highly available

As data becomes more central to businesses, there are more opportunities for compliance violations and a greater risk of breaches. Therefore, data security and privacy have become more critical than ever. Cybersecurity professionals today are effectively entrusted with defending organizations’ data across multiple environments, making the role of a CISO

The dark data industry is rapidly growing, and cyber crimes will only increase in the future. Dark data is generally the data collected as part of compliance but is not effectively used as part of business strategy or marketing. Thus, this type of additional but excessive data that is not












Unlock Your Cyber Security Potential at EC-Council University
"*" indicates required fields
"*" indicates required fields