Digital forensics has moved well beyond the crime lab. Today it serves incident response teams, litigation support, and corporate intelligence. Organizations in finance, healthcare, and tech are building internal forensics capabilities. Law firms hire forensic consultants for e-discovery. M&A advisors bring in forensic analysts during due diligence. The demand is wide and keeps growing. For MSCS students, digital forensics is one of the smartest specializations available. This blog covers the ten skills that matter, the tools behind them, and the career doors they open.
Why Digital Forensics Has Evolved Beyond the Crime Lab
A decade ago, forensics meant disk imaging for law enforcement. That picture has changed. Investigations now span cloud environments, mobile devices, and SaaS platforms. Evidence lives in AWS CloudTrail logs and encrypted iOS backups.
The corporate side is growing fast. Internal investigations, regulatory audits, and insider threat cases all require forensic rigor. M&A due diligence teams use forensic analysts to assess hidden cyber liabilities.
The market reflects this shift. The Bureau of Labor Statistics projects information security analyst roles to grow 29% from 2024 to 2034. That is nearly ten times the average for all occupations. Forensics-specific credentials can add $5,000 to $20,000 to annual salary. Pair them with a master’s degree and that advantage compounds.
The 10 Non-Negotiable Digital Forensics Skills
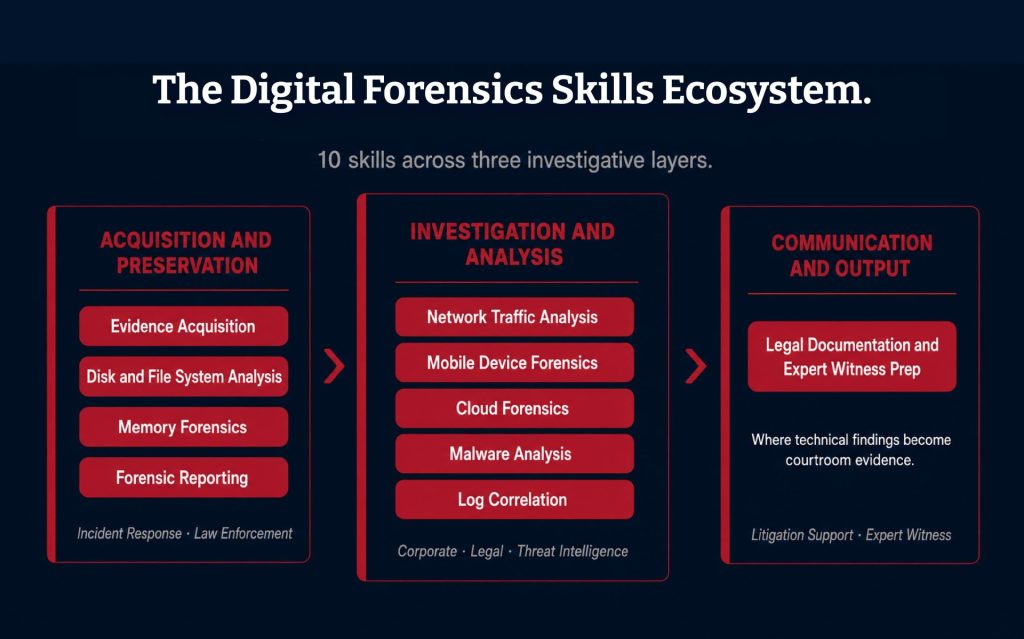
1. Evidence Acquisition and Chain of Custody Preservation
Every investigation starts here. You identify the source, acquire it forensically, and document each step. A broken chain of custody can make evidence inadmissible. The discipline is procedural as much as technical.
2. Disk and File System Analysis
Investigators navigate NTFS, ext4, and HFS+ file systems. Deleted files, slack space, and metadata reveal what active files hide. In ransomware cases, file timestamps can prove when encryption began.
3. Memory Forensics and Volatile Data Recovery
RAM holds evidence that never touches disk. Running processes, network connections, and malware artifacts live in memory. Once a machine powers off, that evidence disappears. Modern attackers often operate entirely in memory to avoid detection.
4. Network Traffic Analysis and PCAP Investigation
Packet captures reveal what moved across a network and when. Analysts use PCAP files to reconstruct attacker behavior and map lateral movement. In litigation, proving what data left the network is often the core question.
5. Mobile Device Forensics
iOS and Android devices carry enormous investigative value. Call logs, location data, deleted messages, and cloud sync records can be recovered. Acquisition techniques differ significantly between platforms. Both matter.
6. Cloud Forensics
This is the fastest-growing area in the field. Investigations increasingly involve AWS CloudTrail, Azure Activity Logs, and Microsoft 365 audit trails. Cloud forensics means knowing which logs exist, where they live, and how long providers retain them. Few analysts have mastered it.
7. Malware Analysis and Anti-Forensics Countermeasures
Malware analysis runs in two modes. Static analysis examines code without executing it. Dynamic analysis runs the sample in a controlled environment. Both are necessary. Antiforensics also falls under this skill. Attackers try to destroy or obscure evidence. Understanding those methods helps analysts recover what was hidden.
8. Log Correlation and Timeline Reconstruction
Investigations rarely rely on one log source. Analysts pull from endpoint logs, firewall records, and authentication systems together. The goal is a clear timeline of what happened and in what order. This is where forensics meets threat intelligence.
9. Legal Documentation and Expert Witness Preparation
Technical skill alone does not close cases. Investigators write reports that hold up under cross-examination. They explain findings to lawyers, judges, and board members. Expert witness preparation is a distinct discipline. It demands clarity and credibility under pressure.
10. Forensic Reporting and Chain of Evidence Documentation
Every investigation produces a deliverable. It must meet legal and organizational standards. Analysts document methodology, findings, and limitations in a reproducible format. Weak documentation has derailed strong cases. This skill protects both the analyst and the organization.
Key Tools Every Digital Forensics Analyst Should Know
Skills need tools to become operational.
Autopsy / Sleuth Kit: These are the open-source standards for disk analysis. It handles file recovery, keyword search, and timeline generation.
FTK (Forensic Toolkit): This is the enterprise choice for forensic imaging. Law enforcement and corporate teams rely on it. Processing speed and indexing capability set it apart.
Volatility: This is the framework for memory forensics. It extracts processes, registry hives, and cryptographic keys from RAM dumps.
Wireshark: This tool handles network capture analysis. It parses PCAP files and supports deep packet inspection.
Cellebrite UFED: This particular tool is the standard for mobile device acquisition. It supports physical, logical, and file system extractions on iOS and Android.
Magnet AXIOM: This tool pulls data from cloud sources, mobile devices, and computers into one investigation workspace.
EnCase: This is a tool built for large-scale enterprise forensics. It integrates evidence management, analysis, and reporting. Corporate and legal teams use it heavily.
Build these skills in a structured, lab-driven environment. Explore the Master of Science in Cyber Security – Digital Forensics at ECCU.
Career Paths and What They Pay
Digital Forensics Analyst: Glassdoor places average total compensation at around $133,000 annually in the US. If you are weighing whether that career trajectory justifies the investment in a Master’s in Digital Forensics, the case is strong.
Incident Response Forensics Lead: This role bridges forensics and crisis management. ZipRecruiter shows average compensation for incident response professionals at $132,962 per year.
e-Discovery Specialist: A professional in this role applies forensic rigor to litigation and regulatory compliance. Demand is strong in law firms and consulting groups.
Threat Intelligence Analyst: These professionals profile threat actors and predict future attacks. A forensics background is a meaningful differentiator here.
Corporate Security Investigator: These are the go-to people who handle insider threats, fraud, and M&A due diligence. ZipRecruiter reports average compensation for cyber investigation roles at around $128,882 annually.

How ECCU's Digital Forensics Specialization Builds These Skills
EC-Council University is a globally accredited online institution. It has over 20 years in cybersecurity education. The MSCS ranks among Fortune’s Top 10 Best Online Master’s in Cyber Security programs. The Digital Forensics track is one of five specializations within the degree.
The program pairs academic rigor with hands-on virtual labs. Students work through realistic investigation scenarios, not just theory. The curriculum covers law enforcement and corporate investigative contexts. Graduates can move across both sectors.
The CHFI certification is embedded through ECCU 502. Students study network intrusion investigation, digital evidence acquisition, and chain-of-custody procedures. ECCU 521 covers mobile forensics. Students learn physical and logical acquisition for iOS and Android.
Students can earn up to four EC-Council certifications alongside the MSCS. These include CHFI, CEH, and CND. A master’s degree plus industry credentials is what forensics hiring managers look for. If you want a detailed breakdown of how to stack certifications and experience as you progress, read How to Become a Digital Forensics Expert. The online format lets working professionals apply learning to active roles immediately.
Ready to build a forensics skill set that holds up in court and in the boardroom? Explore the Master of Science in Cyber Security, Digital Forensics Specialization at ECCU.
Conclusion
Mastering digital forensics is not about collecting certifications. It is about building the mindset that turns raw artifacts into actionable intelligence. The professionals who stand out do not just know the tools. They know how to think through a case, structure findings, and communicate clearly to others. The skills above are the foundation. The tools are the instruments. The right graduate program is where both come together.
FAQs
No. Many forensic professionals come from IT, cybersecurity, or computer science backgrounds. Corporate forensics rarely requires law enforcement experience. Technical competence, analytical thinking, and familiarity with legal evidence standards matter most. A structured graduate program covers all three.
Yes. The Bureau of Labor Statistics projects 29% job growth for information security analysts through 2034. Digital forensics sits within that category. Demand is accelerating as cloud adoption, remote work, and cybercrime volumes all rise simultaneously.
The CHFI is the most directly relevant. The GCFA (GIAC Certified Forensic Analyst) is respected in enterprise environments. EnCE adds value in corporate and legal forensics. CEH rounds out the profile for professionals who want to understand attacker methodology too.
Yes. ECCU’s Digital Forensics specialization covers cloud environments including AWS and Azure forensics. Cloud forensics is one of the fastest-growing sub-disciplines in the field. Programs that include it specifically give you a clear advantage in hiring.