What Is Disaster Recovery in Cybersecurity?
Disaster recovery (DR) in cybersecurity refers to the processes, policies, and technologies used to restore IT systems, data, and operations after a disruptive event. Such events include cyberattacks, natural calamities, infrastructure failures, or geopolitical crises. Organizations today exist in a world where a single disruptive event can halt operations, compromise sensitive data, result in significant fines and penalties, and irreversibly damage their reputation. This is why disaster recovery is essential.
At its core, disaster recovery focuses on two key metrics:
- Recovery Time Objective (RTO): How quickly systems must be restored
- Recovery Point Objective (RPO): How much data loss is acceptable
A well-planned disaster recovery strategy can ensure business continuity even when IT systems are damaged or are entirely offline.

Cybersecurity Implications of Global Disasters
The following disasters can occur on a widespread or international scale, making them interconnected and often amplifying cybersecurity risk for organizations:
- War and Geopolitical Conflict
Conflicts like the Russia-Ukraine war have shown how cyberattacks target critical infrastructure, financial systems, and communications networks.
- Natural Disasters
Floods, hurricanes, and earthquakes can destroy data centers and degrade connectivity. Cybercriminals can take advantage of the ensuing chaos to exploit weaknesses in IT systems.
- Economic Instability
Recessions often lead to reduced cybersecurity budgets, increasing risk exposure, and delaying recovery investments.
- Political Fallout
Sanctions, policy changes, and regulatory shifts can disrupt cloud providers, data sovereignty, and cross-border operations.
Examples of How Disasters Impact Key Industries
- Healthcare: A cyberattack on a healthcare provider during a natural disaster could cripple IT systems, jeopardizing patient care and endangering lives.
- Financial Services: Market instability combined with cyberattacks can halt trading platforms and erode investor confidence.
- Energy and Utilities: Critical infrastructure like energy grids and water treatment plants are usually vulnerable targets. A cyberattack during a storm could delay power restoration efforts.
- Supply Chain and Logistics: Disruptions to seaports, warehouses, or logistics platforms can cascade across global supply chains.
Best Cybersecurity Practices for a Disaster Recovery Plan
A modern disaster recovery plan must factor in various disaster scenarios, be resilient, embrace automation, and be continuously tested. Keep these cybersecurity practices in mind when formulating a disaster recovery plan:

- Adopt a Zero Trust Approach: Ensure that even backup systems are protected against unauthorized access.
- Implement Immutable Backups: Use storage that prevents data from being altered or deleted.
- Leverage Cloud-Based Disaster Recovery: Cloud platforms provide scalability, redundancy, and geographic diversity, which enable faster recovery time.
- Automate Recovery Processes: Automation reduces human error and accelerates recovery time.
- Conduct Regular Testing: Run simulations and tabletop exercises to reinforce the efficacy of your organization’s disaster recovery plan.
- Integrate AI and Predictive Analytics: AI-powered disaster recovery tools can detect anomalies and predict failures before they occur.
- Establish Clear Stakeholder and Communication Protocols: Ensure all stakeholders understand their roles and responsibilities during a crisis, and that constant communication is maintained until full recovery.
Key Elements of a Reliable Disaster Recovery Plan
A well-designed disaster recovery plan should entail:
- Risk assessment and business impact analysis (BIA)
- Clearly defined RTO and RPO metrics
- Data backup and recovery strategies
- Incident escalation procedures
- Vendor and third-party risk considerations
- Compliance and regulatory alignment
Benefits of a Solid Disaster Recovery Plan
Organizations with strong disaster recovery capabilities gain the following benefits:
- Reduced downtime and financial losses
- Improved customer trust and brand reputation
- Compliance with regulatory mandates (HIPAA, GDPR, etc.)
- Operational resilience and agility
- Faster recovery time from cyber incidents and other types of disasters

Why Cybersecurity Professionals Must Understand Disaster Recovery
Cybersecurity professionals must think beyond prevention and focus on resilience. Understanding disaster recovery principles enables them to:
- Design systems that recover quickly from attacks or downtime
- Align cybersecurity operations with business continuity requirements
- Respond swiftly, confidently, and effectively in high-pressure situations
- Protect critical infrastructure and data in the event of a disaster
Core Skills Needed to Become a Disaster Recovery Expert
To specialize in disaster recovery, professionals should develop a blend of technical and strategic skills:
- Risk assessment and business continuity planning
- Cloud architecture and backup solutions
- Incident response coordination
- Threat intelligence and cybersecurity analysis
- Knowledge of compliance frameworks (NIST, ISO 27001)
- Crisis communication and leadership capabilities
- Automation and scripting for recovery workflows
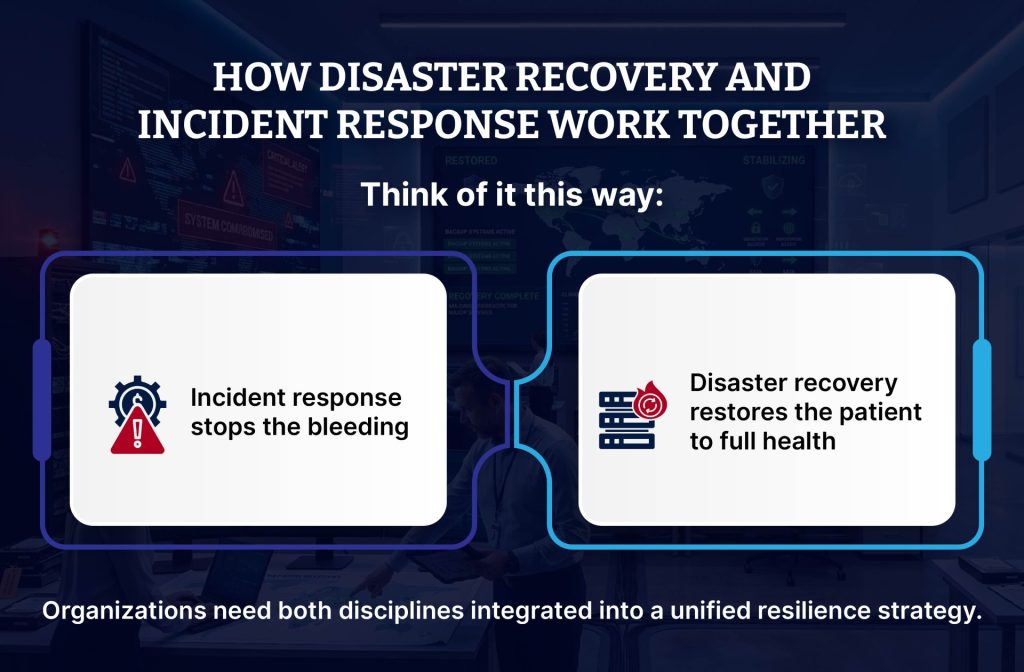
Differences Between Disaster Recovery and Incident Response
| Aspect | Disaster Recovery | Incident Response |
|---|---|---|
| Main Focus | Restoring business operations | Containing and mitigating cyber threats |
| Timing | After a disaster occurs | During or immediately after a cyberattack |
| Primary Objective | Business continuity | Cyber threat elimination |
| Scope | IT systems, data, and infrastructure | Cybersecurity incidents and breaches |
The Future of Disaster Recovery
Looking ahead, disaster recovery will become:
- AI-driven: Automated recovery decisions and predictive resilience
- Cloud-native: Multi-cloud redundancy as a standard
- Cyber-physical: Integration with IoT and critical infrastructure systems
- Regulation-heavy: Governments mandating resilience standards
Organizations that invest now will be better positioned to handle tomorrow’s crises.
How ECCU Equips Cybersecurity Professionals with Disaster Recovery Expertise
EC-Council University (ECCU) offers a specialization in Incident Management and Cyber Operations under our acclaimed Master of Science in Cyber Security program. This specialization provides students with:
- A comprehensive understanding of disaster recovery and incident response practices, principles, and frameworks.
- Extensive hands-on practice using the latest disaster recovery tools in real-world simulations.
- Up to 4 industry-aligned cybersecurity certifications embedded into the coursework, including dedicated certifications in disaster recovery and incident handling.
- Flexibility to study while working, which facilitates real-time application of learnings on the job.
This means that graduates of the program are well prepared to lead in high-pressure environments where resilience in the face of disasters is critical. For more information about the program:
Frequently Asked Questions About Disaster Recovery in Cybersecurity
Disaster recovery in cybersecurity is the process of restoring IT systems, data, and operations after a disruptive event such as a cyberattack or natural disaster.
Disaster recovery minimizes downtime, reduces financial losses, and ensures business continuity during a crisis.
No. Backup involves copying data, while disaster recovery focuses on restoring entire systems and operations.
At least once a year, although high-risk organizations should test their disaster recovery plans quarterly.
RTO stands for Recovery Time Objective, which defines the time required to recover after a disaster. RPO stands for Recovery Point Objective and outlines the acceptable level of data loss after a disaster.
Yes, cloud solutions offer scalability, redundancy, and faster disaster recovery time.
Healthcare, finance, energy, and logistics are among the most critical sectors that need disaster recovery plans.
Gain experience in cybersecurity, learn risk management frameworks, and pursue advanced qualifications, such as ECCU’s master’s degree in cybersecurity (specializing in incident management and disaster recovery) or disaster recovery certification course.