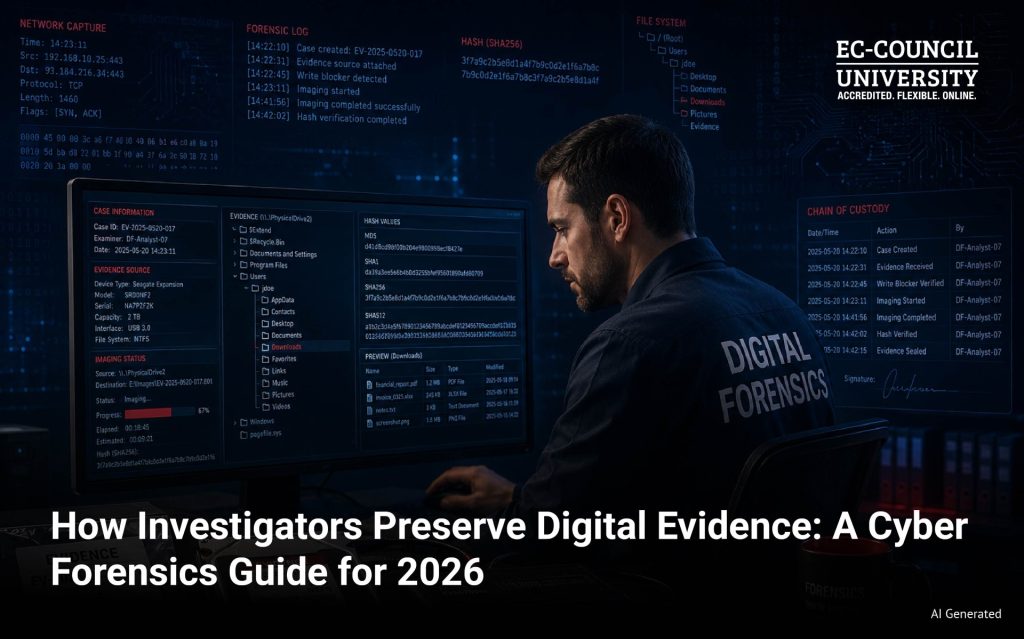
When digital evidence enters an investigation, the clock starts immediately. Every action taken on a device, every file opened, every second of delay changes what investigators can legally use in court.
Cyber forensics is the discipline that governs this process. Digital evidence preservation defines how investigators identify, collect, and preserve digital evidence in a manner that withstands legal scrutiny. But knowing the tools is only part of the job. The protocols matter just as much. A technically sound investigation can still fall apart if the evidence was not handled correctly from the start. This guide walks through how professional investigators preserve digital evidence, why each step exists, and what happens when any part of the process breaks down.
Why Evidence Preservation Is the Most Critical Phase
Preservation is where a cyber forensics investigation either holds together or falls apart. Analysis, reporting, and court testimony all depend on one thing: whether the evidence was handled correctly from the start.
- Digital evidence is fragile: Unlike physical evidence, digital data changes on contact. Opening a file updates its metadata. Running an application writes new data to the drive. Even powering a system off incorrectly can destroy what investigators need most. Edmond Locard’s Exchange Principle applies here: every interaction leaves a trace, and in digital environments, that trace can corrupt the original.
- Contamination rarely starts with the forensics team: First responders, IT staff, or well-meaning employees reach the scene first. They reboot a machine. They delete logs they consider routine. They plug in a USB drive without thinking. By the time trained investigators arrive, the original system state is already compromised.
- The cost of getting it wrong goes beyond the case: IBM’s 2024 Cost of a Data Breach Report found the global average breach cost reached $4.88 million. Poor evidence handling adds to that through dismissed prosecutions, civil liability, and regulatory penalties.
Preservation is not a procedural formality. It is where financial, legal, and investigative outcomes are decided.
Why Digital Evidence Becomes Inadmissible
Courts do not arbitrarily dismiss digital evidence. There are specific, recurring reasons it gets rejected. Understanding them is the first step toward avoiding them in any cyber forensics investigation.
- Broken chain of custody: Any undocumented gap in the chain of custody for digital evidence gives the defense grounds to argue tampering or misidentification.
- Improper handling: Careless forensic evidence handling, opening files, rebooting devices, or using unvalidated tools before acquisition, can alter evidence in ways that cannot be undone.
- Missing hash verification: Without cryptographic proof that the copy matches the original, digital evidence collection cannot be considered complete or court-ready.
- Unauthorized access: Evidence obtained without proper legal authority, a warrant, court order, or provider consent, is inadmissible regardless of what it contains. This also applies to cloud forensics scenarios that require provider authorization.
- Evidence contamination: Introducing foreign data onto a device, even unintentionally, creates doubt about the integrity of everything recovered during digital evidence preservation.
Each of these failures is procedural, not technical. Most are entirely preventable.
The Chain of Custody: What It Is and Why It Matters
The chain of custody is a detailed, chronological record of digital evidence. It documents every person who handled it, every transfer, and every action taken from collection to court. It answers every question a defense attorney will ask: who collected this, when, how, and who has touched it since.
Every transfer of evidence must be logged. Every person who handles a device, image, or storage container must sign off. Chain of custody documentation includes evidence tags, access logs, and hash verification records proving the data was never altered. Modern forensic platforms automate much of this, generating tamper-evident logs and time-stamped audit trails. But automation does not replace documentation discipline. Human entries still need to be accurate and complete.
Step-by-Step: How Investigators Preserve Digital Evidence
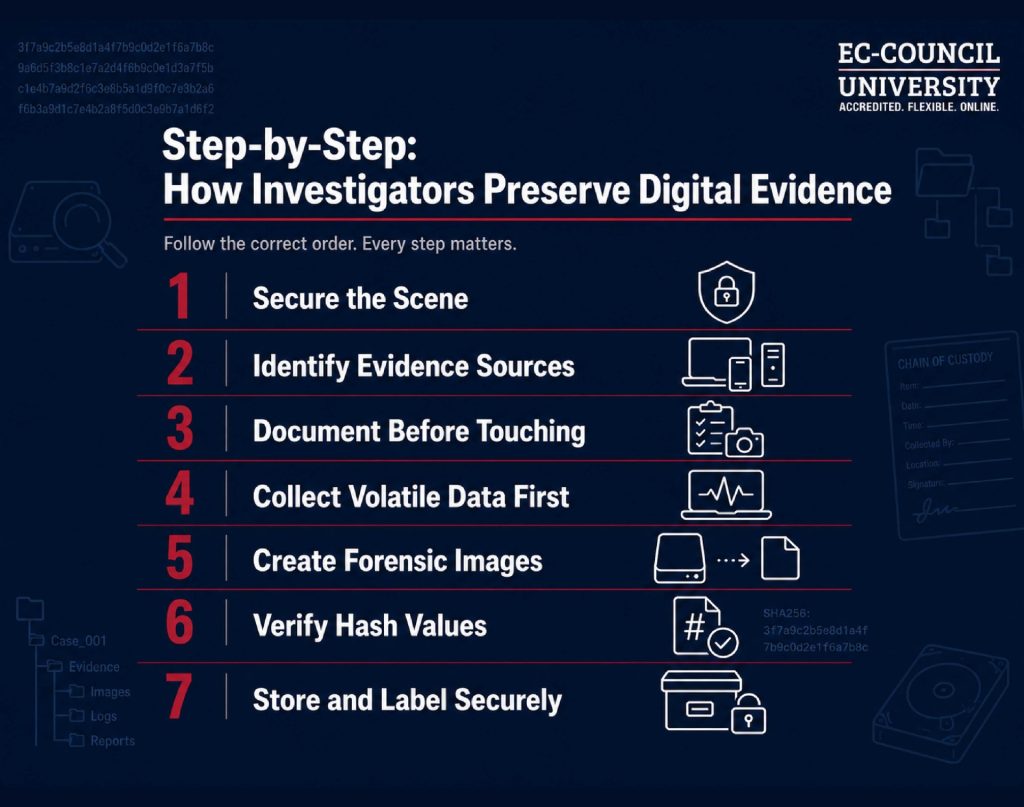
Step 1: Secure the scene
Physical access to devices must be restricted immediately. Faraday bags block wireless signals and prevent remote wiping. Network cables get disconnected where appropriate. Logical isolation comes next: removing a device from the network without shutting it down.
Step 2: Identify all evidence sources
Endpoints, servers, mobile devices, cloud accounts, and network logs are all potential evidence sources. Investigators need a complete inventory before touching anything.
Step 3: Document before touching
Photographs of the physical scene, screenshots of active screens, and network diagrams all happen before any data collection begins. The system state at the moment of discovery is itself evidence.
Step 4: Collect volatile data first
This step is where many investigations go wrong. Volatile data lives in RAM, active processes, and live network connections. It disappears the moment a device loses power. The old practice of pulling the plug was once considered a safe procedure. Digital forensics has since recognized it as destructive. Volatile memory holds encryption keys, running process lists, and active network sessions. None of that survives a shutdown. Investigators now capture RAM images from live systems using specialized tools before any power is cut.
Step 5: Create forensic images
Investigators create bit-by-bit copies of storage devices rather than working on original evidence. Write blockers, either hardware or software, prevent the imaging process from writing anything back to the source drive. Analysis always happens on the copy, never the original.
Step 6: Verify with hash values
After imaging, investigators generate cryptographic hashes of both the original and the copy using MD5 or SHA-256. Matching hash values proves the image is identical to the source. Any future change in the hash signals tampering. This step is non-negotiable for courtroom admissibility.
Step 7: Store and label securely
Evidence gets labeled with case numbers, collection dates, and investigator identifiers. Storage must be access-controlled. Digital chain-of-custody logs record every subsequent interaction.
Every step in this protocol is a skill. Each one can be learned, practiced, and tested before it matters in a real investigation. ECCU’s Graduate Certificate Program in Digital Forensics gives you that practice through hands-on virtual labs built around real forensic scenarios.
Cloud and Mobile Evidence: The New Frontier
Traditional forensics assumes access to physical hardware. Cloud forensics does not have that luxury. In cloud environments, virtual machines can be terminated, storage volumes deleted, and logs rotated quickly. The default log retention period across many cloud providers is 90 days, after which evidence simply ceases to exist unless someone acts to preserve it.
Physical imaging is also impossible in cloud environments. Multiple customers share the same physical infrastructure. Imaging one tenant’s data would expose another’s. Investigators instead work through legal holds, provider cooperation, and snapshot preservation requests. Jurisdictional complexity adds another layer. Data stored across multiple countries means multiple legal frameworks apply simultaneously.
Mobile forensics has its own challenges. Acquisition tools like Cellebrite UFED can extract data from devices, but the source matters. On-device data and cloud-synced data from services like iCloud can differ significantly. App artifacts, cached credentials, and deleted messages may exist in one but not the other. Knowing where to look requires both technical depth and investigative judgment.
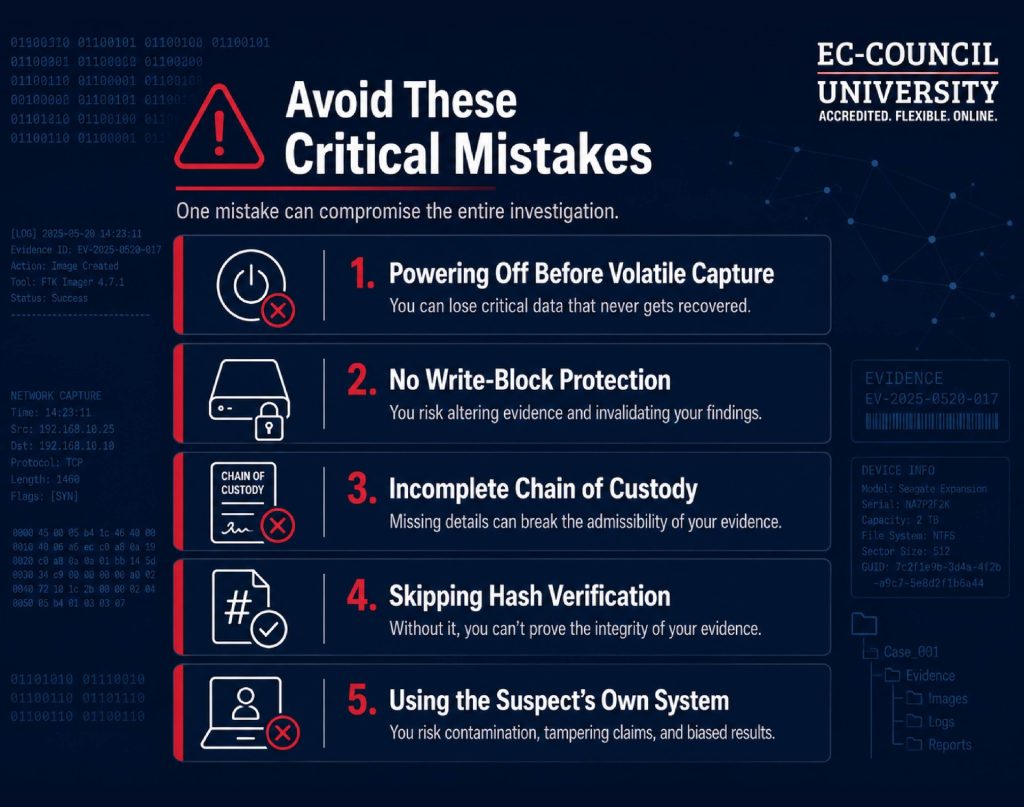
Common Mistakes Forensic Investigators Make
Forensic investigations fail in predictable ways. The mistakes below are not rare or exotic. They show up across cases, industries, and jurisdictions, and almost all of them are avoidable.
- Powering off before volatile capture: RAM contents are gone the moment power cuts. Encryption keys, active sessions, and running processes vanish with them.
- No write-block protection: Any tool that writes back to the source drive risks overwriting the very evidence you are trying to preserve.
- Incomplete chain of custody: Gaps in the evidence log give defense teams exactly what they need to challenge admissibility.
- Skipping hash verification: Without matching hash values, you cannot prove the copy is identical to the original. That proof is what courts require.
- Using the suspect’s own system: This contaminates the evidence and opens the investigator to claims of unauthorized access or tampering.
The pattern behind most of these errors is the same: inadequate training or time pressure at the scene. Both are manageable with the right preparation.
How ECCU's Forensics Curriculum Covers This
Evidence preservation sits at the intersection of law and technology. Technical accuracy matters. Legal defensibility matters equally. A forensic investigator who understands both is significantly harder to discredit in court.
ECCU’s Graduate Certificate program in Digital Forensics is built for working professionals who need this dual competency without committing to a full master’s program. The curriculum spans three focused courses: computer forensics and network intrusion investigation, advanced mobile forensics, and cyber law. That last course matters more than most programs acknowledge. Understanding the legal frameworks around electronic evidence, privacy law, and cross-border jurisdiction is not supplementary knowledge. It is what separates an investigator who can testify effectively from one who cannot. The program also includes the CHFI certification and can be completed in as little as three months.
Conclusion
Digital evidence does not wait. It degrades, gets overwritten, and expires on provider servers. The investigators who get it right are not just technically skilled. They understand why each protocol exists, what breaks when it is skipped, and what that costs in a courtroom. Preservation is not a preliminary step. It is the foundation on which every subsequent phase of an investigation is built on. Get it wrong at the start, and no amount of analysis will fix it. The right cybersecurity education makes the difference between evidence that holds and evidence that doesn’t.
Explore ECCU’s Graduate Certificate Program in Digital Forensics.
Frequently Asked Questions
The chain of custody in digital forensics is a chronological record documenting every person who handled evidence, every transfer it underwent, and every action taken from collection to court. It proves evidence was never tampered with or altered. Courts treat an unbroken chain of custody as a prerequisite for admissibility. In practice, this means signing evidence in and out, logging every access, using tamper-evident storage, and verifying hash values at each stage.
Start by issuing a legal hold or preservation request to the cloud provider immediately. Log retention periods expire fast, sometimes within 90 days, and virtual machines can be terminated without warning. Investigators then obtain the right legal authorizations depending on the jurisdiction. Forensic snapshots replace physical imaging since traditional bit-by-bit acquisition is not possible in shared cloud infrastructure. Every collection step must be documented to establish a defensible chain of custody.
Yes, in many cases they can. Deleting a file removes the reference to it but leaves the underlying data intact until that storage space is overwritten. Forensic tools scan unallocated disk space to recover these remnants. Success depends on the time elapsed since deletion, whether the drive has been written to since then, and the storage type. Recovered files must still meet hash verification and chain-of-custody requirements to be admissible.
Digital evidence must meet four standards: authenticity, integrity, reliability, and legality. Authenticity confirms the evidence is what it claims to be. Integrity proves it was not altered, verified through matching hash values. Reliability means the collection tools and methods are forensically validated. Legality means evidence was obtained through a proper legal authority. The chain of custody must also be complete and unbroken throughout.