Introduction (ICYMI): From Deterrence Breakdown to Continuous Cyber Competition
Before examining how cyber conflict escalates, it’s important to revisit the foundation established in Part 1.
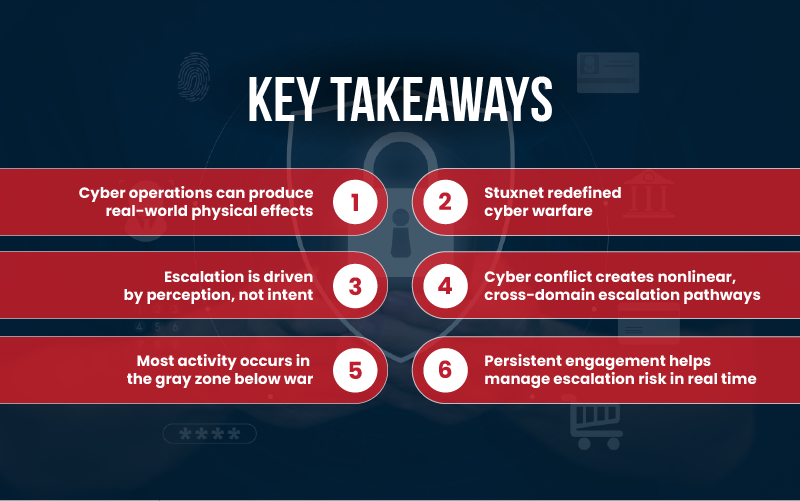
Traditional deterrence theory assumes a world of clarity, where actors can be identified, intentions are visible, and consequences are predictable. In cyberspace, those assumptions begin to break down. Attribution is often delayed or contested, intent is difficult to interpret, and actions frequently occur below the threshold of armed conflict. These conditions create an environment where deterrence struggles to function effectively. Rather than preventing hostile activity, ambiguity encourages it. States are incentivized to operate in the gray zone, pursuing strategic objectives without triggering formal retaliation. This shift transforms cyber conflict from an episodic model of confrontation into one of continuous competition.
In response, states have adopted persistent engagement, a strategy that accepts ongoing interaction in cyberspace and focuses on shaping adversary behavior in real time rather than relying on delayed punishment. But this introduces a new challenge:
If cyber conflict rarely crosses the threshold of war, how does escalation actually occur?
This is where the discussion deepens. Cyber operations may begin quietly, embedded in networks, supply chains, or infrastructure, but their consequences can extend far beyond the digital domain. Once cyber actions intersect with physical systems, economic stability, or national security interests, escalation becomes not only possible but increasingly difficult to predict or control.
Watch Julie Beck’s deep dive episode on cyber conflict, escalation, and persistent engagement:
With that context in mind, Part 2 explores how cyber operations translate into real-world consequences, why perception drives escalation more than intent, and how cyber conflict creates nonlinear pathways into broader strategic confrontation.
Rethinking Escalation in the Cyber Domain
Cyber conflict operates predominantly below the threshold of armed conflict, yet this does not imply the absence of escalation risk. On the contrary, escalation is reconfigured rather than removed.
A central insight is that escalation in cyberspace is driven less by objective intent than by subjective perception. The same intrusion may be interpreted as routine espionage, coercive signaling, or preparation for kinetic action. This interpretive ambiguity compels defenders to default toward worst-case assumptions, thereby increasing the probability of miscalculation.
Moreover, escalation pathways in cyber conflict are inherently nonlinear. Responses frequently manifest across domains (economic sanctions, diplomatic reprisals, or military signaling) rather than remaining confined to cyberspace.
Consequently, even limited cyber operations can generate disproportionate strategic effects.
The Convergence of Cyber and Physical Effects
One of the most consequential developments in cyber conflict is the erosion of the boundary between digital operations and physical outcomes.
The Stuxnet operation stands as a defining case. By targeting industrial control systems at Iran’s Natanz nuclear facility, it demonstrated that cyber capabilities can induce physical destruction while maintaining a degree of plausible deniability.
This operation achieved three critical effects:
- Manipulation of industrial processes
- Physical degradation of critical infrastructure
- Deception of human operators through falsified system feedback
In doing so, it decisively refuted the notion that cyber conflict is inherently nonviolent or limited to the virtual domain.
Frequently Asked Questions
Yes. The Stuxnet attack demonstrated that cyber operations can manipulate industrial systems and cause real-world physical destruction.
Escalation is driven more by perception than intent. If an action is perceived as threatening critical systems or national security, it can trigger significant responses, even if the original intent was limited.
Cross-domain escalation occurs when a cyber incident triggers responses in other areas, such as economic sanctions, diplomatic retaliation, and military action. Cyber conflict rarely stays confined to the digital domain.
Cyber escalation lacks a clear “ladder” or sequence. Because actions are ambiguous and interconnected, small incidents can rapidly trigger large and unexpected consequences.
Persistent engagement manages escalation risk by increasing visibility into adversary actions, disrupting threats early, and minimizing the element of surprise. It focuses on managing conflict proactively rather than reacting after escalation.