Why SIEM is Critical for Cybersecurity in 2026
If you’ve spent any time around cybersecurity teams, you’ve probably heard the term ‘SIEM’ thrown around constantly. But the problem is that most people think SIEM is just a logging tool. It’s not.
SIEM, short for Security Information and Event Management, is the backbone of modern Security Operations Centers (SOCs). It enables organizations to collect, analyze, and act on security data in real time, turning raw logs into actionable intelligence. In today’s volatile threat landscape, this capability is essential and underscores why SIEM remains one of the most foundational (and misunderstood) cybersecurity technologies.
Let’s break it down in plain terms.
What Is SIEM? (A Simple Explanation)
In essence, SIEM is a cybersecurity solution that:
- Collects log data from across an organization’s IT environment
- Aggregates and normalizes that data
- Analyzes events for suspicious activity
- Generates alerts for potential threats
Think of SIEM as the central command center for your organization’s security data. Instead of checking logs manually across dozens (or hundreds) of systems, SIEM brings everything together into a single, unified view.
How SIEM Works: A Step-by-Step Breakdown
To really understand SIEM, you need to understand what’s happening under the hood. Here’s what a typical SIEM process entails:
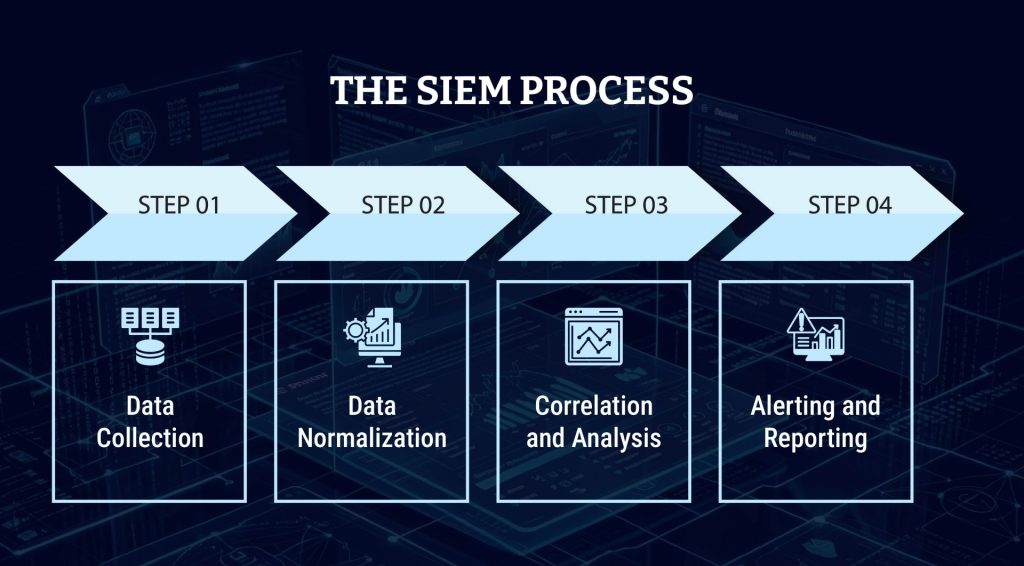
Step 1: Data Collection
SIEM platforms ingest data from multiple sources, including:
- Firewalls
- Servers
- Endpoints
- Applications
- Cloud services
This can amount to terabytes of data daily in large enterprises.
Step 2: Data Normalization
Different systems generate logs in different formats. SIEM tools standardize this data so it can be analyzed consistently.
Step 3: Correlation and Analysis
This is where SIEM becomes powerful. The system correlates events across different sources to identify patterns. For example:
- Multiple failed login attempts
- Followed by a successful login from a new location
- Followed by unusual data access
Individually, these events may seem harmless. Together, they signal a potential breach.
Step 4: Alerting and Reporting
When suspicious activity is detected, SIEM generates alerts for SOC analysts. It also provides dashboards and reports for:
- Compliance
- Auditing
- Executive visibility
Key Features of Modern SIEM Solutions
SIEM tools have evolved significantly. In 2026, modern-day platforms offer:
- Real-Time Monitoring: Continuous visibility across networks, endpoints, and cloud environments.
- Advanced Threat Detection: Using behavioral analytics and machine learning to identify anomalies.
- Log Management: Centralized storage and retrieval of logs for investigations and compliance.
- Compliance Reporting: Supports frameworks like GDPR and PCI DSS.
- Integration with Other Tools: Modern SIEM integrates with SOAR platforms, threat intelligence feeds, and endpoint detection tools.
Why Organizations Need SIEM
Without SIEM, most organizations are basically operating in the dark when it comes to cybersecurity. Here’s why SIEM matters:

- Faster Threat Detection: SIEM reduces the time to detect threats by automatically correlating events.
- Centralized Visibility: Instead of fragmented data, security teams get a single pane of glass.
- Improved Incident Response: SIEM provides the context analysts need to respond quickly and effectively.
- Regulatory Compliance: Many organizations must retain, monitor, and report data logs for regulatory purposes. SIEM simplifies all of this.
Common Challenges of SIEM
It would be fair to say that SIEM isn’t perfect, as it brings up the following challenges:
- Alert Fatigue: One of the biggest issues. SOC teams can face thousands of alerts daily, many of which are false positives.
- Complex Implementation: Deploying and tuning a SIEM system requires skilled professionals and significant time investment.
- High Costs: Licensing, storage, and maintenance can be expensive, especially for large organizations.
- Data Overload: More data doesn’t always mean better security. Without proper tuning, SIEM can become overwhelming rather than helpful.
SIEM vs XDR vs SOAR: What’s the Difference?
This is a question many people have, so let’s simplify it:
| Category | SIEM | XDR | SOAR |
|---|---|---|---|
| Primary function | Collects, aggregates, and analyzes log data for threat detection | Detects and responds to threats across multiple security layers (endpoint, network, cloud) | Automates security workflows and incident response actions |
| How it works | Ingests logs from various sources and applies rules/analytics to generate alerts | Correlates telemetry across tools to identify and stop threats in real time | Uses playbooks to automate investigation and response processes |
| Main Benefit | Centralized visibility and event correlation | Deep, integrated threat detection with contextual insights | Automation and orchestration of repetitive tasks |
How SIEM Fits into the Modern SOC
In today’s SOC environment, SIEM is part of an ecosystem of cybersecurity solutions rather than being a standalone tool. It works in tandem with:
- Threat intelligence platforms
- Automation tools
- Incident response systems
SIEM is thus a core pillar of a fully integrated SOC workflow.
This video helps you understand effective SOC management:
The Future of SIEM: What’s Changing?
Key trends shaping the future of SIEM include:
- AI-Driven Analytics: Machine learning is improving threat detection accuracy and noise reduction.
- Cloud-Native SIEM: Modern SIEM solutions are moving to the cloud, which offers greater scalability, faster deployment, and lower infrastructure costs.
- Integration with Automation (SOAR): Reducing manual effort and accelerating response times.
- User and Entity Behavior Analytics (UEBA): Detecting insider threats and compromised accounts through behavioral patterns.
How AI and ML Are Transforming SIEM
AI and ML (machine learning) have shifted SIEM from rule-based detection to intelligent, adaptive security. Traditional SIEM relied heavily on predefined rules, like essentially “if this happens, trigger an alert.” That approach still exists, but it’s no longer enough to keep up with sophisticated threats. Today’s attackers are stealthier, faster, and often use legitimate tools to avoid detection. That’s where AI and ML come in.
- Behavioral Analytics and Anomaly Detection: Modern SIEM platforms use User and Entity Behavior Analytics (UEBA) to determine a baseline of what “normal” activity looks like across users, devices, and systems. ML models continuously refine this baseline and flag deviations like unusual login times, abnormal data transfers, or unexpected access patterns. This allows SIEM to detect unknown threats and insider activity, not just known attack signatures.
- Smarter Event Correlation and Alert Prioritization: AI dramatically improves how SIEM correlates events. Instead of analyzing alerts in isolation, it connects thousands of signals across the environment and assigns risk scores based on context. The result is fewer false positives, more meaningful alerts, and faster decision-making for analysts. AI also helps prioritize alerts, ensuring SOC teams focus on what actually matters instead of drowning in noise.
- Automated Investigation and Faster Response: In 2026, AI-powered SIEM can not only detect threats but also investigate and respond to them. AI helps summarize incidents and highlight root causes, recommend response actions, and trigger automated workflows when integrated with SOAR. For high-confidence threats, some systems can even automatically initiate response actions, significantly reducing response times.
- Predictive and Proactive Security: The biggest shift is that SIEM is no longer purely reactive. By analyzing historical data, behavioral trends, and threat intelligence, AI-enabled SIEM can predict potential attack paths, identify vulnerable assets, and detect early indicators of compromise. This moves security operations toward a proactive, prevention-focused model.
- Human + AI = The New SOC Model: Despite all these advancements, AI isn’t replacing SOC Analysts. It’s augmenting them. AI brings speed, scalability, and pattern recognition across massive datasets, while humans bring context, critical thinking, and strategic decision-making. The most effective SOCs in 2026 combine both, using AI to handle volume and complexity, and analysts focus on high-value investigations.
Why SOC Professionals Must Upskill
What many companies overlook is the fact that SIEM is only as effective as the people managing it. To truly leverage SIEM, cybersecurity professionals need skills in:
- Log analysis
- Threat detection
- Scripting and automation
- Cloud security

This is where education becomes critical. At EC-Council University (ECCU), we focus on upskilling professionals to leverage technologies such as SIEM in real-world SOC environments. Our online cybersecurity degrees and certification courses emphasize:
- Hands-on practice with the latest cybersecurity tools
- Industry-relevant qualifications and credentials
- Real-world SOC scenarios you’ll encounter on the job
Find out more about the ECCU upskilling experience:
Final Thoughts: Is SIEM Still Relevant in 2026?
The short answer is a resounding “yes”. Despite the rise of newer technologies like XDR and SOAR, SIEM remains the foundation of security operations. But the key takeaway is that SIEM is not a “set it and forget it” tool. To be effective, it requires:
- Continuous tuning
- Skilled SOC Analysts
- Integration with modern technologies
Organizations that treat SIEM as a strategic capability, not just a compliance checkbox, are the ones that stay ahead.
Frequently Asked Questions About SIEM in Cybersecurity
SIEM stands for Security Information and Event Management. It is a cybersecurity solution that collects, analyzes, and correlates security data from across an organization’s IT environment. SOC professionals rely on SIEM to detect and respond to potential threats in real time.
The primary purpose of a SIEM system is to provide centralized visibility into security events, enabling organizations to detect threats faster, investigate incidents efficiently, and maintain compliance with regulatory requirements.
SIEM improves threat detection by correlating data from multiple sources, identifying patterns of suspicious behavior, and generating alerts for potential security incidents that might otherwise go unnoticed.
SIEM is a technology platform, while a Security Operations Center (SOC) is a team or function that uses tools like SIEM to monitor, detect, and respond to cybersecurity threats.
Yes, SIEM remains highly relevant in 2026. It continues to serve as the foundation of modern security operations, especially when integrated with advanced technologies like XDR, SOAR, and AI-driven analytics.
Key benefits of SIEM include real-time threat detection, centralized log management, improved incident response, and support for compliance and auditing.
Common challenges associated with SIEM include high implementation and maintenance costs, alert fatigue from false positives, complex configuration and tuning, and the need for skilled cybersecurity professionals.
Professionals working with SIEM should have skills in log analysis and event correlation, threat detection and incident response, basic scripting (Python), and an understanding of networks, cloud environments, and security frameworks.