Hackers no longer need to break through firewalls. They just need to ask the right person the right question. According to the FBI, in 2024, the United States lost $16.6 billion to social engineering attacks. That is a 33% jump from the year before. Globally, online scam losses crossed $1 trillion in a single year. The numbers are staggering. But the bigger story is the
method. Attackers are targeting people, not systems. And people, unlike software, cannot be patched.
Social engineering is now the top initial access method in cybersecurity breaches. Between May 2024 and May 2025, 36% of all cyber intrusions began with a social engineering tactic. It surpassed malware, exploits, and every other breach vector. If you are building a career in cybersecurity, understanding this threat is not optional.
Source: FBI Internet Crime Report 2024 and Cybercrime Magazine
What Is Social Engineering?
Social engineering is a manipulation technique that tricks people into divulging confidential information or granting access. It does not rely on technical vulnerabilities. It exploits human instincts: trust, urgency, fear, and helpfulness. An attacker does not hack your system. They convince someone inside your organization to open the door for them.
Why Social Engineering Attacks Are So Effective?
The human brain is not built for constant suspicion. Attackers exploit this. They trigger emotional
responses that override rational thinking. Urgency is a common weapon. So is authority. When
someone appears to be a senior executive or IT support, people comply quickly. Remote work
has made this worse. Digital communication removes body language cues. Verification
becomes harder. Attackers also do their homework. Publicly available data on LinkedIn,
company websites, and social media arms them with enough context to sound legitimate. Add AI into the mix, and phishing emails now take under five minutes to craft. They are personalized,
polished, and nearly impossible to distinguish from real ones.
What Are the Most Common Types of Social Engineering Attacks?
- Phishing: This is the most widespread. Attackers send deceptive emails to steal
credentials or install malware. In Q1 and Q2 of 2025 combined, over two million phishing attacks were recorded. (Source: Anti-Phishing Working Group) - Pretexting: This involves creating a fabricated scenario to extract information. An attacker might impersonate HR, IT, or an auditor.
- Baiting: This method uses curiosity as bait. Infected USB drives left in a parking lot or fake downloads online are classic examples.
- Quid pro quo: An attacker offers something in return for information. A fake IT helpdesk
offering to “fix your system” in exchange for your login is one example. - Tailgating: This vicious method is physical in nature. An attacker follows an authorized
employee into a restricted area. - Vishing and smishing: These techniques use phone calls and SMS, respectively. Vishing attacks surged 442% in the second half of 2024. By 2025, voice phishing had overtaken email as the primary social engineering vector. (Source: Security Magazine)
- MFA fatigue: In these attacks, attackers flood users with push notifications until they approve one, out of sheer exhaustion. This technique has been used to bypass multi
factor authentication in high-profile enterprise breaches.
Social Engineering Attacks: Real-World Examples That Made Headlines
Social engineering attacks do not stay theoretical for long. These three recent cases show exactly what happens when attackers exploit human trust at scale.

How to Spot a Social Engineering Attack?
Social engineering attacks rarely announce themselves. Here are the warning signs that should immediately put you on alert:
- Something feels off: Trust that instinct. Social engineers are skilled at making the abnormal seem routine.
- Unsolicited requests for credentials or access: No legitimate system or colleague needs your password.
- Unusual urgency or pressure: Attackers manufacture panic to short-circuit rational thinking.
- Someone claiming authority over sensitive systems: Always verify through a
separate, known channel. - Unexpected MFA push notifications: If you did not initiate a login, reject it immediately.
- Unfamiliar attachments in familiar-looking emails: Check the sender address carefully before you click anything.
How to Prevent Social Engineering Attacks?
The good news is that social engineering attacks are preventable. Organizations that successfully defend against these cyber-attacks share one thing in common: they do not rely on a single measure. These are the building blocks of a solid defense:
- Employee Awareness and Training: Simulated phishing tests and regular training keep people sharp. Organizations with trained employees detect attacks faster.
- Strong Authentication Measures: MFA adds friction that attackers cannot easily overcome. Be aware that it is not foolproof against MFA fatigue attacks.
- Verify Every Request: Never act on requests involving sensitive data or system access without confirmation. Establish a clear callback protocol for identity verification.
- Email and Communication Security: Use tools that filter known malicious senders and flag suspicious patterns. Use them consistently, not selectively.
- Limit Information Sharing: Oversharing on social media and professional networks hands attackers ready-made reconnaissance material.
- Organizational Policies: Define what is shareable, who has access to what, and how sensitive requests get escalated. Put it in writing.
Can Technology Stop Social Engineering Attacks?
Technology can detect, filter, and flag. AI-based threat detection identifies unusual login behavior before it escalates. Email filtering tools stop phishing attempts at the gateway. Endpoint security monitors devices for signs of compromise. Browser-level tools flag ClickFix style fake alerts that trick users into executing malicious commands.
So, can technology stop social engineering attacks? Not entirely. The human element is a factor in 60% of all data breaches, and no algorithm can replace judgment in the moment. Technology narrows the window of opportunity for attackers. Training and awareness close it.
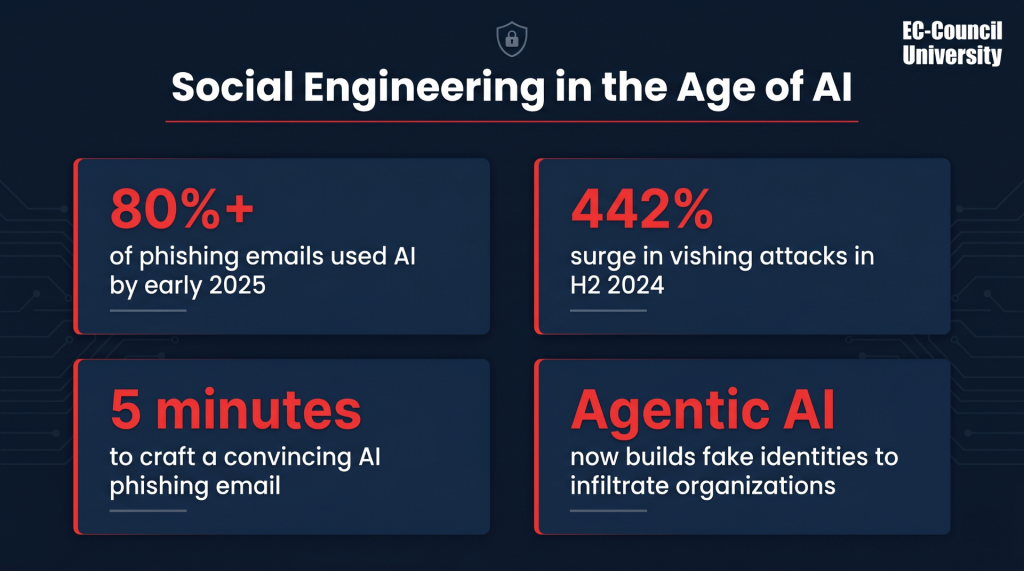
Social Engineering in the Age of AI
AI has not just changed how we communicate. It has changed how attackers operate. The
numbers below show just how fast that shift is happening:
- 80%+ of phishing emails were AI-generated by early 2025 (Source: Security Magazine)
- Vishing attacks surged 442% in the second half of 2024 (Source: Security Magazine)
- A convincing phishing email now takes under 5 minutes to craft using AI
- Agentic AI is now being used to build fake identities and infiltrate organizations
Why Cybersecurity Education and Career Readiness Matter
Social engineering is not a niche threat. It is the dominant attack method of our time, and it is
getting more sophisticated by the day. Security analysts, IT professionals, and business leaders
all need to understand it. Knowing how attackers think is no longer a bonus skill. It is a baseline requirement.
The demand for cybersecurity professionals who understand human-centric attacks is rising
fast. Social engineering succeeds because it exploits what makes us human, and defending against it requires both education and technology working together. Knowing the threat is the first step. Being trained to act on that knowledge is what separates a target from a defender.
That training is exactly what ECCU’s Master of Science in Cyber Security and other programs are built for. Hands-on labs, industry-recognized certifications, and a curriculum built around real threats prepare you for the roles that matter.
To learn more about cybersecurity education at ECCU:
Frequently Asked Questions
A social engineering attack is a manipulation technique that tricks people into divulging confidential information or granting unauthorized access. Unlike traditional cyberattacks, it does not exploit technical vulnerabilities. It exploits human instincts such as trust, urgency, and fear to bypass security controls.
The most common types of social engineering attacks are phishing, pretexting, baiting, quid pro quo, tailgating, vishing and smishing, and MFA fatigue. Each type exploits a different human instinct, from curiosity to authority to exhaustion. Understanding how these attacks work is the first step to recognizing them before they succeed.
Preventing social engineering attacks requires a combination of employee training, strong
authentication measures, and clear organizational policies. No single measure is enough on its own. Simulated phishing tests, callback verification protocols, and strict information-sharing guidelines together significantly reduce your exposure.
Social engineering attacks are effective because they target human psychology rather than technical systems. Attackers exploit emotional triggers such as urgency, authority, and fear to override rational thinking. The rise of AI-powered phishing and deepfake technology has made these attacks faster, more personalized, and significantly harder to detect.
One of the most high-profile recent examples is the Coinbase breach in May 2025, in which
attackers bribed overseas support staff to leak sensitive customer data, including names,
birthdates, and partial Social Security numbers. Coinbase refused a $20 million ransom demand and offered a counter-bounty for information leading to the attackers. This case demonstrates that even well-resourced organizations are vulnerable when the human layer of security is compromised.