Penetration testing is one of those careers that sounds clear from the outside. You simulate attacks. You find vulnerabilities. You get paid well to think like a hacker. But the moment you try to actually enter this field, the path gets murky fast. Which penetration testing certification comes first? Do you need a degree? How do you get experience when every job asks for experience? This blog answers those questions in the order they actually matter.
What Is Penetration Testing?
Penetration testing is the authorized practice of simulating real-world cyberattacks against an organization’s systems to find exploitable vulnerabilities before malicious actors do. It is not a passive scan or a checklist exercise. It is an active, structured attempt to breach security controls under controlled conditions.
The meaning of penetration in this context is precise: gaining access through security boundaries using the same techniques and thinking a real attacker would. That is what separates pen testing from every other security assessment.
What Pen Testers Actually Do
Forget the Hollywood image of a hooded hacker. Real pen testing is methodical, documented, and deeply collaborative. A pen tester’s week looks like this: scoping calls with clients, reconnaissance, active scanning, exploitation attempts, and detailed penetration testing report writing. The job is about 40% technical execution and 60% communication. You find a vulnerability. Then you explain it to a non-technical executive. Both pen tester skills matter equally.
No two engagements are identical. One week you are testing a hospital’s network. The next, you are social engineering a financial institution’s front desk staff. Adaptability is the real skill. Tools are just instruments.
Want to understand why organizations actually commission these tests? Read Why Do We Need Penetration Testing?
Penetration Testing Career Fundamentals: The Three Pillars You Must Build First
Most beginners skip the foundation-building of pen tester skills and jump straight to tools. That is the fastest way to plateau your career early.
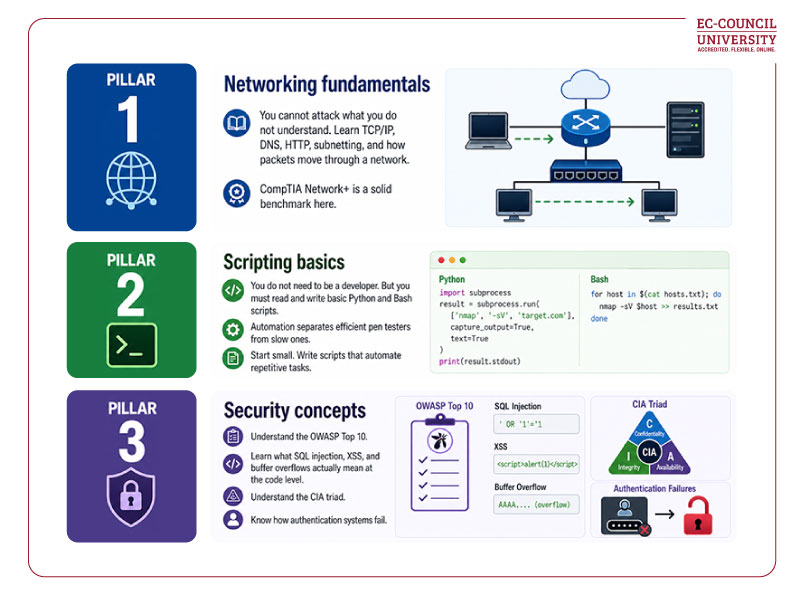
These three pillars are non-negotiable. Every advanced pen tester skill you build later sits on top of them.
Many beginners also carry assumptions about this field that slow them down. This piece on popular pen testing misconceptions is worth reading.
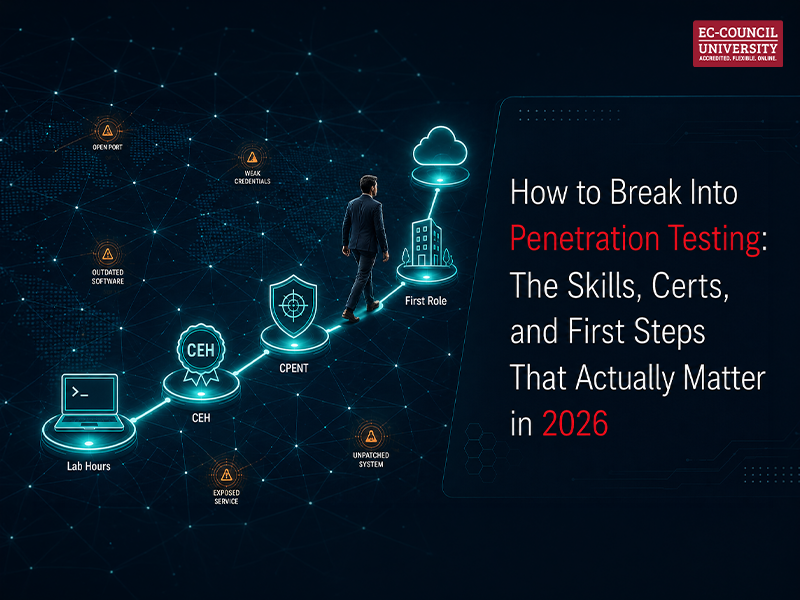
The Penetration Testing Learning Path: From Zero to First Role
There is a logical sequence to this journey. Skipping steps is how people spend years learning without becoming hireable.
Step 1: Build lab experience before anything else
Platforms like TryHackMe and HackTheBox offer structured, beginner-friendly environments. Spend 90 days here before touching certifications. Document every machine you compromise. Treat it like a work portfolio.
Step 2: Earn your first credential
Ethical Hacking and Countermeasures with CEH (Certified Ethical Hacker) certification is the widely recognized entry point for an ethical hacker career path. It signals foundational knowledge to employers. It also builds the vocabulary you need for advanced certifications later needed for a pen tester.
Step 3: Move toward specialist-level certification
Conducting Penetration And Security Tests with CPENT (Certified Penetration Testing Professional) is where real differentiation happens. It covers advanced network penetration, IoT testing, OT systems, and binary exploitation. It is a practical, performancebased exam. Passing it signals you can operate in real environments, not just controlled labs.
Step 4: Build in parallel, not sequentially
Do not wait until you are certified to build your portfolio. Write about what you learn. Post write-ups of TryHackMe rooms. Contribute to bug bounty programs on HackerOne or Bugcrowd. Even modest public work builds credibility faster than certifications alone.
Penetration Testing Tools You Will Use on the Job
Employers do not expect you to master every tool before your first role. They expect comfortable familiarity with the core stack.
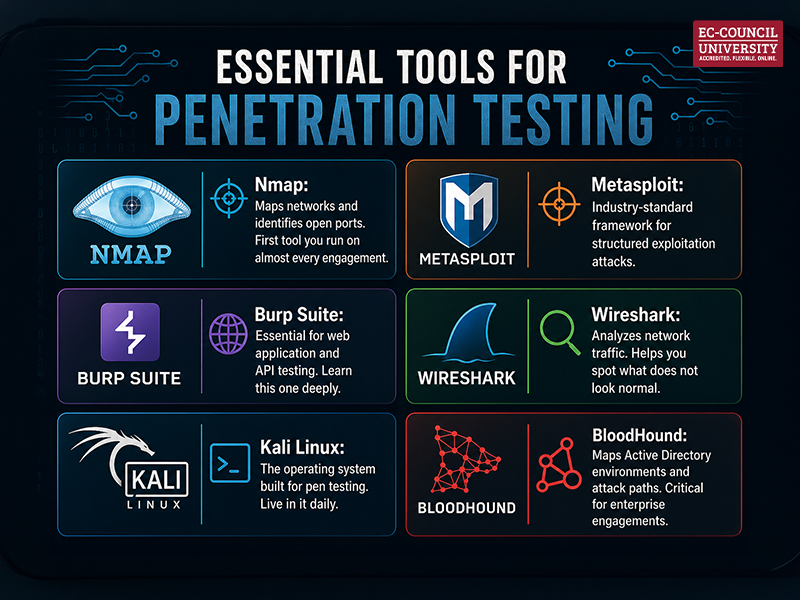
These pen-testing tools and associated technologies are evolving rapidly, especially as AI enters the picture. Watch our video below to see where penetration testing is heading.
How to Become a Penetration Tester
When you are considering a full-fledged penetration testing career , self-study takes you far. A structured penetration testing certification program takes you further, faster.
ECCU’s Conducting Penetration and Security Tests is a 10-week, online, 3-credit-hour non-degree course. It is built for working professionals. You do not need to commit to a full degree to enroll. The curriculum covers all major pen test types, OSINT, social engineering, and enterprise network testing, with virtual lab exercises throughout.
It feeds directly into the CPENT certification path, giving you both academic grounding and a recognized industry credential.
Salary at Each Penetration Testing Career Stage
The financial case for this career is strong and getting stronger.
The US Bureau of Labor Statistics projects a 33% increase in information security analyst roles between 2023 and 2033. That is nearly three times faster than the average across all US occupations. The global pen testing market is projected to grow 24% through 2026, driven by tightening compliance requirements and expanding attack surfaces.
Here is what the pay looks like at each stage, per Glassdoor’s April 2026 data:
- Junior Penetration Tester: $142,602 average annually. Entry point, but already well above the national median.
- Mid-Level Penetration Tester: $154,208 average annually. You are leading engagements and mentoring junior testers.
- Senior / Principal Consultant: Top earners reach $206,047 at the 75th percentile, with the 90th percentile crossing $265,000.
- Bug Bounty (Supplemental): Skilled hunters on HackerOne and Bugcrowd report earning anywhere from $500 to $50,000 per critical vulnerability. It is not a salary replacement, but it is real income running in parallel.
Conclusion
Penetration testing is not a career you fall into. It is one you build deliberately, layer by layer. The good news is that the field is actively looking for people willing to do that work. Roles are open. Salaries are strong. And the demand is not plateauing anytime soon.
Start with the foundations. Log the lab hours. Earn your credentials in sequence. And when you are ready to accelerate, find a program that combines real instruction with hands-on practice.
Explore ECCU’s Non-Degree Penetration Testing course and CPENT certification path.
Frequently Asked Questions
Yes, penetration testing is completely legal when conducted with explicit written authorization from the system owner. Without that authorization, the same actions become a criminal offense under laws like the Computer Fraud and Abuse Act in the US. Every legitimate engagement begins with a signed scope agreement that defines what can be tested, when, and by whom. Organizations commission these tests precisely because they have a compliance requirements and a security mandate to meet. The authorization document is what separates an ethical pen tester from a malicious actor.
Start with free lab platforms like TryHackMe and HackTheBox before anything else. These give you structured, hands-on practice without needing a live target. Document every exercise you complete. Build a GitHub portfolio of your write-ups and scripts. Then pursue CEH as your first formal credential. From there, CPENT is the performance-based penetration testing certification that demonstrates real-world capability to employers. Experience and credentials built in parallel will get you hired faster than either one alone.
CEH (Certified Ethical Hacker) is the recognized starting point. It establishes foundational knowledge and gives you the vocabulary for everything that follows. After CEH, CPENT is the specialist-level credential that covers advanced network penetration, IoT, OT systems, and binary exploitation. For professionals who want structured academic grounding alongside certification prep, hands-on penetration testing training through ECCU’s nondegree course builds both simultaneously. Certifications signal competence. The practical hours and the pen tester skills behind them are what actually make you hireable.
It depends entirely on scope. A focused web application test can be completed in two to three days. A full enterprise network engagement, covering internal infrastructure, Active Directory, and social engineering, can run two to four weeks. Scoping calls at the start of every engagement exist precisely to set this timeline. The broader the attack surface, the longer the test. And a longer test means a more detailed pen test report with more findings, more remediation recommendations, and more value delivered to the client.
A vulnerability assessment scans your systems and produces a list of known weaknesses. It does not attempt to exploit them. A penetration test goes further. It actively tries to exploit those weaknesses to determine whether they are genuinely dangerous in a real attack scenario. One tells you what might be wrong. The other tells you what an attacker could actually do with it. The distinction matters because many vulnerabilities that look critical on a scan turn out to be unexploitable in practice, and vice versa. There are also common misconceptions about pen testing that blur this line further, particularly around what black-box and white-box testing actually involve.