
Top Entry-Level Cybersecurity Roles After Your Bachelor’s or Master’s Degree
Cyber threats are growing at a fast pace, and so is the demand for specialized and skilled cybersecurity professionals. So, for those of you looking
Our unique program allows our graduates to lead their peers to strategically and effectively manage cybersecurity risks in their organizations.


Cyber threats are growing at a fast pace, and so is the demand for specialized and skilled cybersecurity professionals. So, for those of you looking

In the world of the Internet and digitization, passwords are the first line of defense between your digital assets and cybercriminals. Yet weak or reused passwords remain among the most significant reasons behind data breaches,

Healthcare Data: What it is and Why it’s Important to Protect it Healthcare data is among the most sensitive categories of information. It includes electronic
What Are Military Tuition Assistance and GI Bill® Education Benefits? For U.S. Military members and veterans, education benefits can dramatically reduce or eliminate the cost

What Are Cybersecurity Certifications? Cybersecurity remains one of the most critical and future-proof career paths available today. Whether you’re a seasoned cybersecurity professional looking to

Cybersecurity has become one of the most critical and in-demand career fields across industries. Cybersecurity is no longer a niche reserved for large tech companies.

Cybersecurity Jobs are More Important Than Ever The cybersecurity industry is experiencing unprecedented growth — and for good reason. Organizations worldwide constantly face complex digital

Why Should You Get a Master’s in Cybersecurity Degree in 2026? Cybercrime has become almost a daily reality. As we move deeper into 2026, organizations

Protecting Energy Infrastructure Requires a Multi-Pronged Approach As the energy sector undergoes a rapid digital transformation, cybersecurity resilience has become a crucial factor in ensuring
Evolving Cybersecurity Threats in the Energy Sector The energy sector has emerged as one of the most targeted industries in the global cyber threat landscape.
Quishing is not an emerging threat anymore. It is here, and it is scaling fast. What started as a fringe attack technique has quietly grown
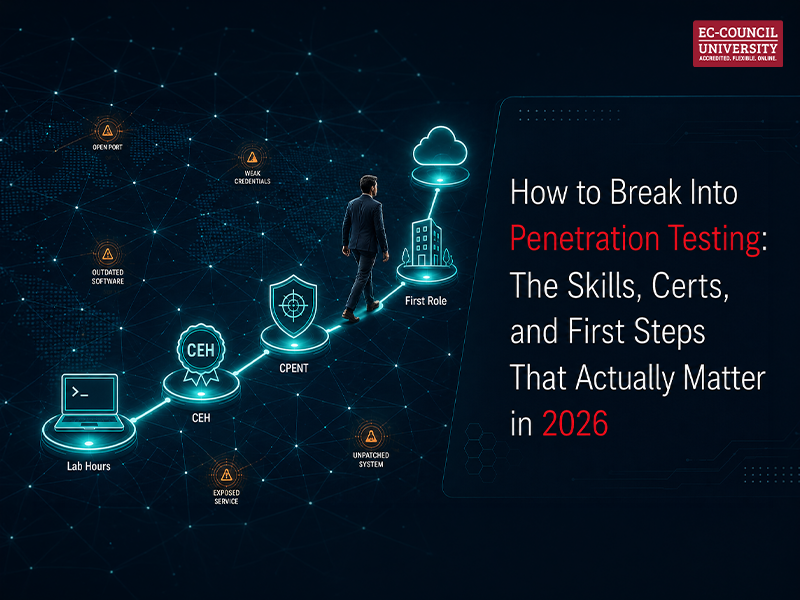
Penetration testing is one of those careers that sounds clear from the outside. You simulate attacks. You find vulnerabilities. You get paid well to think

The Rise of Prompt Injection as a Cybersecurity Threat As organizations race to embed large language models (LLMs) into customer service platforms, enterprise tech stacks,

Cybersecurity is not a static field. It never was. But the pace at which AI is reshaping it has forced a specific question for anyone

Why Cryptocurrency Needs Cybersecurity Cryptocurrency was built on the promise of decentralization, transparency, and trustless transactions. But in reality, while the blockchain technology that underpins cryptocurrency is inherently secure, the ecosystem surrounding

A master’s degree is a significant commitment. For working professionals, the first question is rarely “should I do this?” It is “can I actually fit
Why SIEM is Critical for Cybersecurity in 2026 If you’ve spent any time around cybersecurity teams, you’ve probably heard the term ‘SIEM’ thrown around constantly.

A Degree Dilemma: Cybersecurity or Computer Science? If you’re at the start of your career or thinking about switching paths, you’ve probably run into a

Hackers no longer need to break through firewalls. They just need to ask the right person the right question. According to the FBI, in 2024,
An Overview of VA Chapter 31 Leaving the military is a major life transition. If you’ve been through it (or are about to), you already
"*" indicates required fields
There are 1,757 data breaches each minute. By the time you finish reading this article, thousands of data breaches will have occurred. A person, organization, or government directs most. Local governments struggle to keep up with new technologies for better service in exchange for the risk of a cyber attack....
Responding to cyber threats has become a high priority for organizations of all sizes, especially those in financial services. Cybersecurity is a vital element in preventing cyberattacks, as established in the good practices report published by the Financial Industry Regulatory Authority (FINRA). It is an institution that regulates the activity....
In the rapidly evolving digital landscape, cybersecurity has emerged as a critical concern for organizations across all industries. Understanding and addressing cybersecurity risks is essential for protecting data and ensuring the resilience and continuity of business operations. As a faculty member specializing in human resources, change management, and business continuity....
Introduction The growth of multi-cloud adoption, in conjunction with the need to secure different workloads and deployment from code to cloud, led companies to start looking for a unified solution that could consolidate many siloed capabilities that were offered by cloud security posture management (CSPM) platforms, cloud workload protection (CWP)....
Prof. Christopher R. Barnhart Department of Cyber Security, EC-Council University Cybersecurity has been described as a sub-topic of “I.T.” Cybersecurity differs from other I.T. roles because it is focused on enforcement instead of compliance. Cybersecurity professionals must work in an ever-changing environment, with multiple threats and constantly changing rules and....
There is no doubt that we live in a new stage of Humanity. We are immersed in a different reality than a few decades ago. Artificial Intelligence (AI) is present everywhere. Whenever we use computers or any other digital device, we use AI. The advancement of robotics is incredible. Astonishing....

The demand for cybersecurity professionals has reached unprecedented heights. With the constant proliferation of cyber threats and the crucial need to safeguard sensitive data, there’s a significant shortage of skilled cybersecurity experts. You’re on the right track if you’re considering a career in this dynamic field. This blog is your

1. How does cloud technology help to secure a remote workforce compared to traditional on-premises solutions? Cloud technology has the ability to adapt quicker to changes needed to secure workloads. It can spin up new services/servers to account for increased load during demand. It can also be more highly available

As data becomes more central to businesses, there are more opportunities for compliance violations and a greater risk of breaches. Therefore, data security and privacy have become more critical than ever. Cybersecurity professionals today are effectively entrusted with defending organizations’ data across multiple environments, making the role of a CISO

The dark data industry is rapidly growing, and cyber crimes will only increase in the future. Dark data is generally the data collected as part of compliance but is not effectively used as part of business strategy or marketing. Thus, this type of additional but excessive data that is not











Unlock Your Cyber Security Potential at EC-Council University
"*" indicates required fields
"*" indicates required fields