In today’s digital age, the term “data breach” is increasingly making headlines, and its consequences can be severe. This blog will demystify the notion of data breaches, explain their implications, and provide comprehensive guidance on what companies and individuals should do in the aftermath of such incidents.
What is a Data Breach?
A data breach transpires when unauthorized individuals gain entry to, disclose, or steal sensitive and confidential information. These breaches can take various forms, including cyber attacks, insider threats, or accidental data exposure. In essence, a data breach compromises the integrity and security of data, and the potential harm extends far beyond the stolen information itself.
Data breaches can target a wide range of information, including personal data, financial records, intellectual property, etc. Cyber criminals often seek this data to exploit it for financial gain, identity theft, corporate espionage, or even politically motivated actions. By understanding the nature of data breaches, individuals and organizations can competently defend themselves against these dangers.
What Are the Potential Outcomes of a Data Breach?
The repercussions of a data breach are significant for individuals and organizations. Companies may suffer financial losses, damage to their reputation, and legal liabilities. The breach can result in identity theft, financial fraud, or other malicious activities for individuals. The sheer scale and sensitivity of the data exposed in a breach can lead to many negative consequences.
For organizations, data breaches can lead to severe financial losses, legal consequences, and damage to their reputation. Customers and partners may lose trust, and recovery can be lengthy and costly. Data breaches are often preventable through robust cybersecurity measures and proactive risk management.
The societal implications of data breaches include the erosion of privacy, a chilling effect on free speech, and impacts on innovation and economic growth. As technology advances, the battle against data breaches will remain ongoing, with cybersecurity professionals, organizations, and governments working together to protect sensitive information and maintain the trust of individuals and society.
What Should a Company Do After a Data Breach?
- Retain the Breach: The first step is to isolate and limit the damage by shutting down compromised systems, networks, or accounts. This prevents further unauthorized access and protects unaffected parts of the organization.
- Notify Affected Parties: Companies must promptly inform affected individuals, customers, or partners about the breach, detailing what information was compromised. Transparency is crucial in rebuilding trust and maintaining legal compliance.
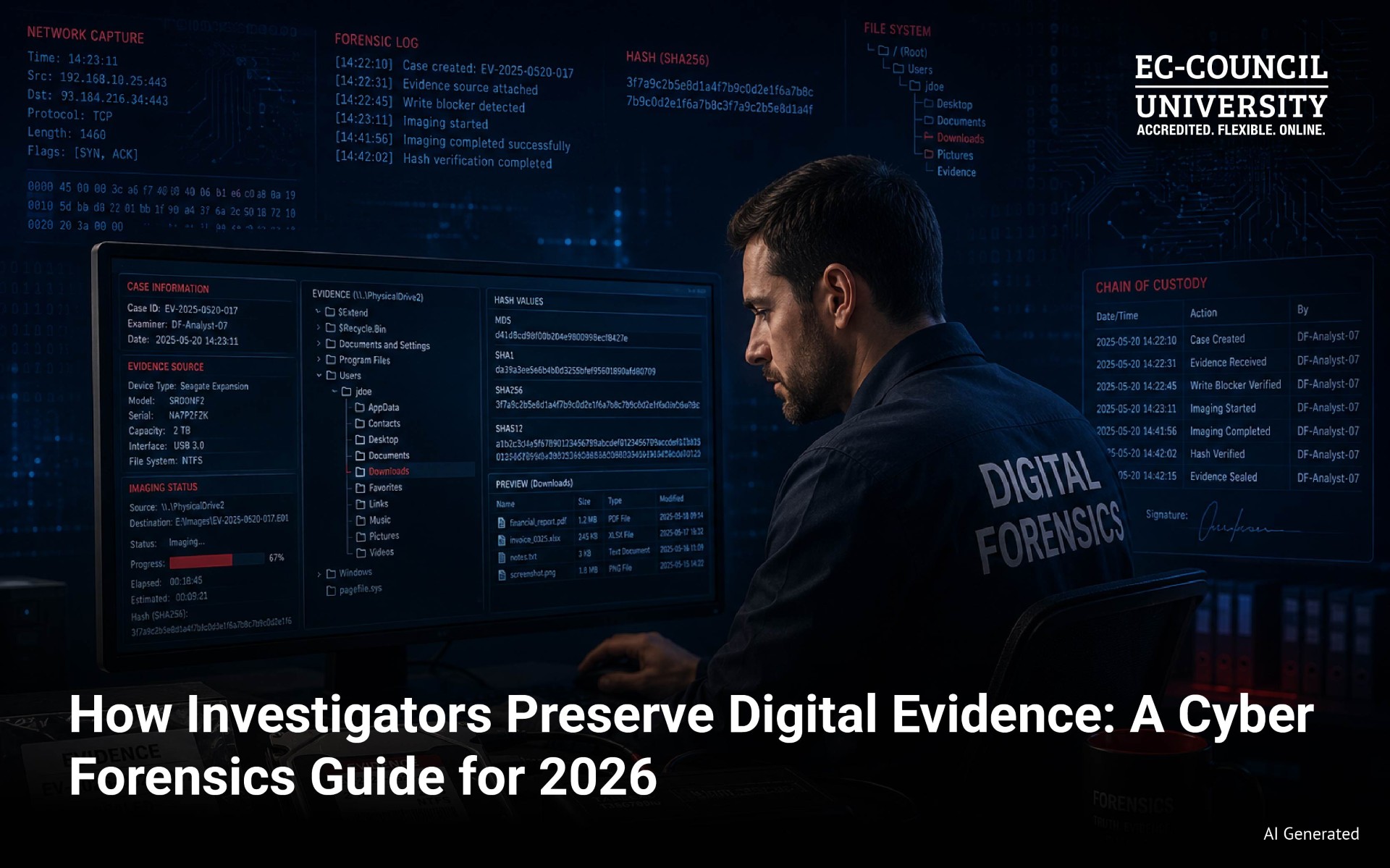
- Preserve Evidence: Preserving evidence for legal and investigative purposes is essential. This includes logs, timestamps, and other relevant data that can assist in tracking the breach’s origin and impact. This evidence may be essential in pursuing legal action or identifying the responsible parties.
- Conduct a Thorough Investigation: Identifying the root cause of the breach is essential to preventing future incidents. A comprehensive investigation can help determine the exploited vulnerabilities and the necessary measures to patch them.
- Implement Security Improvements: Based on the investigation findings, companies should implement security improvements to prevent similar breaches in the future. This may involve updating security protocols, enhancing employee training, and fortifying network defenses.
What to Do After a Data Breach
For individuals:
- Monitor Accounts: Regularly check financial accounts, credit reports, and online activities for suspicious or unauthorized transactions. Early detection can help minimize the damage caused by identity theft or financial fraud.
- Change Passwords: Immediately change passwords for any affected accounts and enable two-factor authentication where available. Strong, unique passwords are a fundamental line of defense against unauthorized access.
- Stay Vigilant: Be cautious about unsolicited communications, such as emails or phone calls. Cyber criminals often use phishing techniques to exploit individuals affected by a breach. Confirm the legitimacy of any communication before transferring sensitive information.
- Consider Freezing Your Credit: If you suspect your personal information is at risk, you can try to freeze your credit. This makes it difficult for potential identity thieves to open new accounts in your name.
Data breaches are a growing concern today. Understanding a data breach, recognizing its implications, and knowing how to respond are crucial for individuals and companies. By taking proactive measures and following the right procedures, the impact of a data breach can be minimized, and data can be safeguarded against future threats. Organizations need to invest in robust cybersecurity measures and for individuals to stay vigilant in protecting their personal information.
In an era where data is a valuable currency, safeguarding it has never been more critical. By being informed and prepared, we can collectively lower the dangers associated with data breaches.
How Can EC-Council University Help You Understand Data Breach
EC-Council University offers a comprehensive range of degree programs to address data breach prevention, detection, and response intricacies. The curriculum includes cutting-edge courses such as the Certified Ethical Hacker (C|EH), Certified Network Defender (C|ND), and Computer Hacking Forensic Investigator (C|HFI), among others, all of which are essential for understanding and mitigating the risks associated with data breaches. These courses cover various aspects of cybersecurity, including offensive and defensive tactics, risk management, digital forensics, and incident response. EC-Council University’s commitment to providing top-notch education and certifications in cybersecurity is a vital resource in preparing individuals to combat data breaches effectively. With their specialized courses, students can develop the expertise and skills required to safeguard data, networks, and systems from the ever-present threat of data breaches.