Re-examining the Cybersecurity Breach Narrative
Cybersecurity is often framed as a constant battle between organizations and sophisticated attackers lurking in the dark corners of the internet. Headlines about “hackers breaking in” grab news headlines, leading people to believe that cybersecurity failures are almost always the result of external intruders exploiting vulnerabilities. But the reality is far more nuanced and troubling. A growing body of research shows that most breaches aren’t caused solely by hackers, but by failures within an organization. Addressing this reality requires a blend of technical expertise and strategic leadership.
An overwhelming majority of organizations still assume that an external hacker will be the root cause of their next breach. However, multiple recent reports paint a very different picture:
- According to a 2025 study, 95% of data breaches had some elements of human error that contributed to the incident.
- Studies find that insider threats, including negligent or compromised employees, contractors, or partners, play a role in about 35–50% of breaches, with a large proportion due to unintentional mistakes rather than malicious intent.
- In many cloud breach reports, configuration mistakes and human oversight are primary factors, not exotic exploits or highly advanced external attacks.
These facts challenge the “malicious hacker” storyline and reinforce the need to focus on internal systems, processes, and behavior.
Real-World Breach Example Rooted in Internal Failures
The Capital One Data Breach (2019)
One of the most high-profile breaches influenced by internal issues (even if an attacker ultimately gained access to sensitive data) is the Capital One data breach. While a former employee of a cloud solutions provider was convicted in relation to this breach, the root cause was not a sophisticated exploit against Amazon’s AWS infrastructure. Rather, it was an error in how Capital One configured its cloud firewall and permission policies that enabled an attacker to exploit a server-side request forgery (SSRF) vulnerability to access data stored in AWS buckets. A misconfigured web application firewall (WAF) inadvertently provided more access than necessary, and monitoring controls failed to detect it quickly.
This incident underscores that even the most capable technology stack can be undermined by simple misconfigurations and governance gaps.
The Real Causes of Most Cybersecurity Breaches
While external hackers play a role in many cybersecurity breach incidents, a deeper look reveals that systemic vulnerabilities within organizations are the primary enablers.
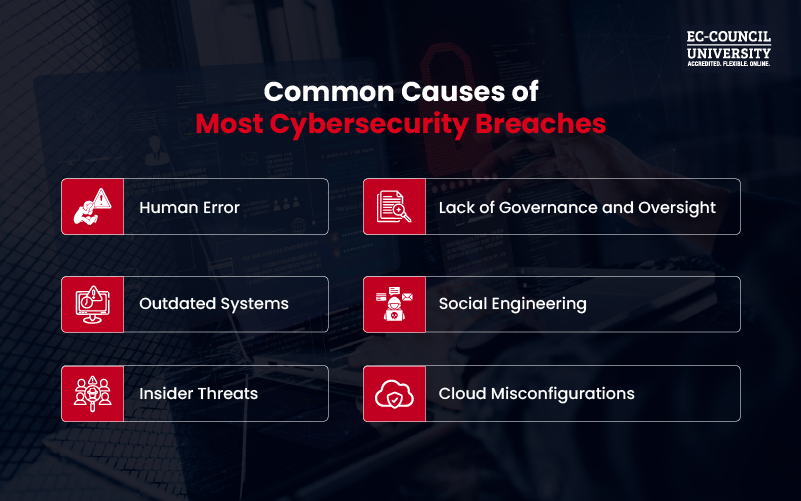
- Human Error: Humans remain the weakest link in most cybersecurity chains. Reports consistently show that a vast majority of cybersecurity incidents involve human error, whether it’s falling for a phishing attack, mishandling credentials, or misconfiguring systems. Even security professionals can be victims of the same cognitive biases and workload pressures as other employees, making error‐proofing systems essential.
- Outdated Systems: Legacy servers, unpatched software, and unsupported applications are a massive risk. Threat actors don’t need to be sophisticated. Instead, they pinpoint outdated infrastructure and exploit known vulnerabilities. Ongoing maintenance and lifecycle management are therefore non-negotiable parts of effective cybersecurity.
- Insider Threats: Internal actors, whether malicious or inadvertent, have legitimate access to systems. According to industry analyses, insider threats contribute to roughly half of all cybersecurity breaches, with negligence accounting for the majority. This is not limited to disgruntled employees. Contractors, partners, and third-party vendors with insufficient oversight can often introduce novel risk vectors to critical systems.
- Lack of Governance and Oversight: Security isn’t just about technology. It’s about process, policy, and leadership. Weak governance frameworks, unclear accountability, and poor risk management practices create gaps that neither firewalls nor endpoint detection systems can cover. When roles aren’t defined, when escalation paths aren’t clear, and when board-level reporting is weak, organizations essentially operate blind.
- Social Engineering: Social engineering remains one of the most effective ways for attackers to bypass security controls. Whether via phishing, vishing, smishing, or pretexting, attackers target human psychology and often succeed because humans are not perfect. Security awareness training and instilling a cybersecurity culture throughout an organization are critical to resisting these tactics.
- Cloud Misconfigurations: Cloud adoption has accelerated, but so have breaches caused by misconfigurations. A misconfigured database or an overly permissive access policy can expose terabytes of sensitive information, and attackers know this. Cloud providers emphasize that security is a shared responsibility, meaning the organization controls key aspects of configuration and access.
What Cybersecurity Professionals Must Do to Mitigate These Risks
To effectively reduce cybersecurity breaches, professionals must develop a holistic and strategic approach that addresses both human and technical factors:
- Comprehensive Security Awareness: Provide cybersecurity awareness training to all employees, not just IT teams. Practices such as phishing simulations, role-based security training, and integrating cybersecurity KPIs into performance goals help boost organizational resilience.
- Robust Patch and Change Management: Automated patching, scheduled vulnerability scans, and strict change control processes reduce the risk of outdated systems and unknown vulnerabilities.
- Identity and Access Governance: Implement least-privilege access, strong authentication (MFA), and regular access reviews to prevent misuse of credentials, no matter where they originate.
- Cloud Security Best Practices: Cloud security requires more than tooling. It requires secure cloud architecture, continuous configuration monitoring, and threat detection tailored to individual cloud environments.
- Insider Threat Programs: Behavioral analytics, zero-trust segmentation, privileged access monitoring, and clear escalation procedures help detect and respond to internal risk signals before a breach incident can occur.
- Alignment Between Cybersecurity Practices and Business Objectives: Cybersecurity should be a core business imperative, not a technical afterthought. Leaders must be engaged and informed, and actively promote cybersecurity best practices across every function and department.
How ECCU’s MSCS Degree Prepares Professionals for Modern-Day Threats
At EC-Council University (ECCU), we recognize that cybersecurity is not just a purely technical discipline. It also involves understanding human behavior, governance, risk management, cloud-native threats, and strategic leadership.
That’s why the curriculum of our Master of Science in Cyber Security program goes beyond sharpening technical expertise to turn students into cybersecurity leaders. The program offers 5 specialization options, each designed to enable learners to design and implement frameworks that prevent systemic failures. Additionally, the program also embeds globally recognized certifications into the curriculum, such as:
- Certified Ethical Hacker (CEH)
- Computer Hacking Forensic Investigator (CHFI)
- Certified Network Defender (CND)
- Certified Penetration Testing Professional (CPENT)
- Certified Cloud Security Engineer (CCSE)
- EC-Council Certified Incident Handler (ECIH)
- Certified Chief Information Security Officer (CCISO)
- And more!
These certifications validate essential skills for understanding both internal and external threats. By bridging the gap between technical proficiency and strategic insight, ECCU graduates are equipped to lead organizations in closing the gaps that cause most cybersecurity breaches.
In Summary
The common misconception that “hackers are most to blame” obscures the fact that cybersecurity breaches are often systemic failures rooted in human behavior, outdated systems, misconfigurations, governance gaps, and insufficient oversight. External attackers are opportunists. They rarely need to engineer an exploit when internal cybersecurity lapses or neglect can leave the door wide open.
To reduce breaches, we must shift the focus from the dark alleyways of the internet to boardrooms, IT processes, and human behavior within organizations. ECCU’s Master of Science in Cyber Security (MSCS) program prepares professionals to lead this shift with the technical mastery and governance acumen needed to safeguard today’s complex tech-driven enterprises.
To know more about the MSCS program:
Frequently Asked Questions
Recent research shows that most breaches involve internal failures, such as misconfigurations and human error.
An insider threat is a cybersecurity risk posed by people within an organization, such as employees, contractors, or partners, who have legitimate access.
Cloud misconfigurations remain one of the most common and damaging breach vectors, often due to human error.
Security awareness training significantly reduces risk by helping staff resist phishing and social engineering attacks.
Governance provides cybersecurity policies, accountability, and risk oversight, which are fundamental to preventing systemic failures.







